Cyber security consulting provides businesses with strategic guidance and technical expertise to protect critical assets like data, operations, and reputation. It is an essential investment in a company's resilience, designed to identify financial and operational risks from cyber threats and build a practical roadmap to manage them effectively.
For business leaders, this service translates complex technical vulnerabilities into clear business impacts, helping you make informed decisions about security investments. A consulting partnership focuses on proactive defense, moving your organization away from a reactive "break-fix" model toward a mature security posture that supports long-term growth and maintains client trust.
What Is Cyber Security Consulting for a Business?

Many business leaders view cyber security as a technical issue handled by an internal IT team or a managed service provider. While these teams are vital for daily operations, their primary focus is on system uptime and performance. Cyber security consulting operates at a more strategic level, focusing on risk management and business resilience.
An effective analogy is to think of a consultant as a structural engineer for your digital infrastructure. Your IT team acts as the general contractor, building and maintaining the structure. The engineer, however, identifies hidden weaknesses, stress points, and environmental risks that could lead to a catastrophic failure. They provide the expert analysis and roadmap needed to reinforce your digital foundations.
The Shift from Reactive Fixes to Proactive Strategy
For years, many businesses addressed security only after an incident occurred. This reactive approach is no longer viable in today's threat landscape. Modern cyber threats are too sophisticated and damaging for a "fix-it-when-it-breaks" model.
A data breach is not a simple technical problem; it is a business crisis that can trigger significant financial losses, regulatory penalties, and irreversible damage to client trust. A consulting partnership shifts an organization's posture from reactive to proactive, focusing on identifying and mitigating risks before they can be exploited.
A proactive security strategy is a fundamental requirement for operational resilience and client confidence. The goal is to build a defense strong enough to deter attackers and robust enough to ensure business continuity.
Core Objectives of a Consulting Engagement
A successful cyber security consulting engagement is an ongoing partnership designed to mature your security posture over time. Its objectives are tied to tangible business outcomes, ensuring every recommendation supports your company's broader goals. For more details on tailored approaches, explore our guide on cybersecurity for small businesses.
This table breaks down how a typical engagement delivers value.
Key Components of a Cyber Security Consulting Partnership
| Engagement Phase | Primary Objective | Key Business Outcome |
|---|---|---|
| Discovery & Assessment | Identify and quantify business risks | Clear visibility into vulnerabilities and their potential financial impact. |
| Strategic Planning | Develop a tailored security roadmap | A prioritized, budget-conscious plan to address the most critical risks first. |
| Implementation & Hardening | Strengthen defenses and close security gaps | Reduced attack surface and improved protection for critical data and systems. |
| Ongoing Management | Maintain and mature the security posture | Continuous improvement, compliance assurance, and operational resilience. |
Ultimately, the partnership focuses on four key objectives:
- Identify and Quantify Risk: Pinpoint vulnerabilities in technology and processes and translate them into potential business impact.
- Achieve and Maintain Compliance: Navigate complex regulations like PIPEDA or industry-specific mandates to avoid fines and legal issues.
- Strengthen Defenses: Implement the right mix of technology, policies, and training to protect against common and advanced threats.
- Build a Resilient Operation: Ensure the business can withstand and quickly recover from a security incident with minimal disruption.
Core Services in a Consulting Engagement

A genuine cyber security partnership delivers practical services that address real-world business risks. Each service is designed to protect revenue, maintain client trust, and enable stable, secure growth.
These core services are the building blocks of a resilient security posture. They provide clarity on weaknesses, defend against emerging threats, and ensure operations align with critical industry regulations.
Risk Assessments and Penetration Testing
You cannot secure what you do not understand. A risk assessment provides a 360-degree view of your business—from technology and processes to people—to identify security gaps. It answers the crucial question: "Where are we most vulnerable, and what is the business impact of an incident?"
Penetration testing (pen testing) is a practical exercise where authorized ethical hackers attempt to breach your systems, simulating the actions of a real attacker. This controlled simulation uncovers vulnerabilities that a standard review might miss, demonstrating precisely how a threat actor could access your critical data.
Think of a risk assessment as the blueprint inspection of your digital building. Penetration testing is the real-world stress test to see if the locks and alarms hold up under pressure. Both are necessary to confirm your defenses are solid.
When engaging in these services, it is crucial to have formal contracts, like a Penetration Testing Agreement, that clearly define the scope and deliverables.
Managed Detection and Response
You cannot fight a threat you cannot see. Managed Detection and Response (MDR) provides 24/7/365 monitoring of your network, servers, and endpoints by a dedicated team of security experts. It functions like an outsourced security operations center (SOC) without the significant cost and complexity of building one in-house.
Unlike traditional antivirus software, which reacts to known threats, MDR actively hunts for suspicious behavior that could indicate a sophisticated attack. When a potential threat is detected, the MDR team investigates, contains it, and initiates a response to neutralize it. This rapid intervention prevents minor alerts from escalating into major data breaches.
Compliance and Governance
Navigating regulations like PIPEDA, GDPR, or industry-specific mandates in sectors like law or healthcare can be a major challenge. A single compliance failure can lead to substantial fines, reputational damage, and lost business.
Cyber security consulting translates complex legal requirements into a practical, actionable security plan. This typically involves:
- Gap Analysis: Measuring your current security controls against regulatory requirements to identify shortfalls.
- Policy Development: Creating and implementing the formal security policies and procedures that regulators require.
- Audit Preparation: Preparing your organization for official audits, ensuring you can confidently demonstrate compliance.
This process is about building a sustainable governance program that integrates security and compliance into daily operations. You can learn more about protecting sensitive information in our article on advanced cybersecurity frameworks.
Virtual CISO Services
Many small and mid-sized businesses need executive-level security leadership but cannot justify the cost of a full-time Chief Information Security Officer (CISO). A Virtual CISO (vCISO) provides this strategic guidance on a fractional, more cost-effective basis.
Your vCISO acts as a senior member of your leadership team, responsible for developing and overseeing your entire security program. They translate technical risks into business terms for the board, manage the security budget, and align the security strategy with your company’s growth goals. This service bridges the critical gap between technical execution and high-level business strategy.
How to Choose the Right Cyber Security Partner
Selecting a cyber security consultant is a critical business decision. The right partner becomes a trusted advisor and an extension of your team. The wrong one can lead to wasted investment and a false sense of security.
The objective is to find a firm that goes beyond a simple vendor relationship and understands your business. This means looking past technical certifications and focusing on their ability to connect security measures to your operational and strategic goals. A great partner delivers clarity and confidence, helping you navigate complex risks in plain business language.
Evaluating Industry-Specific Experience
Cyber security needs vary significantly by industry. A manufacturing company faces different threats and compliance requirements than a law firm or a healthcare clinic. Generic, one-size-fits-all security plans often fail to address the industry-specific vulnerabilities that attackers exploit.
When vetting potential partners, ask for specific examples of their work with businesses similar to yours. A consultant with deep experience in the legal sector, for example, will already be familiar with the unique confidentiality and data governance rules your firm must follow. This specialized knowledge ensures their recommendations are not only technically sound but also practical, relevant, and compliant with your industry’s standards.
Questions to Ask About Industry Expertise
To assess a potential partner’s understanding of your industry, ask direct questions:
- Case Studies: "Can you share anonymized case studies or examples of how you have helped other companies in our industry solve specific security challenges?"
- Compliance Knowledge: "What is your experience with the compliance frameworks that govern our business, such as PIPEDA or specific healthcare data privacy laws?"
- Relevant Threats: "What are the most significant cyber threats currently targeting businesses in our sector, and how does your approach defend against them?"
Their responses will reveal whether they possess the specialized experience required to protect your unique environment.
Assessing Communication and Business Acumen
Technical expertise is a baseline requirement. The key differentiator is the ability to communicate risk in clear business terms. Your consultant must be able to explain complex threats—and their potential financial or operational impact—to your leadership team without relying on technical jargon.
A consultant's true value lies in their ability to translate technical vulnerabilities into business risk. If they cannot clearly articulate why a specific security control matters to your bottom line, they are not the right strategic partner.
During the evaluation process, pay attention to how they answer your questions. Do they focus on technical details or business implications? A true strategic advisor will always connect their recommendations to your core priorities, such as risk reduction, operational continuity, and client confidence. This business-first communication is the hallmark of a mature consulting practice. For additional context, our guide on managed IT services can provide a helpful framework.
Focus on Scalable Solutions and Predictable Costs
Finally, a strong partner will offer solutions that can scale with your business and have a clear, predictable cost structure. Avoid engagements based on hourly rates, which can become unpredictable and expensive, particularly during a crisis.
Instead, look for firms that offer fixed-fee arrangements for services like managed detection and response or vCISO guidance. This model aligns their incentives with yours—their goal is to keep you secure and stable, not to accumulate billable hours. Ask potential partners how their engagement models support long-term growth and provide the budget certainty needed for effective planning.
Finding the Right Engagement Model
Choosing a cyber security partner is one step; determining the financial and operational structure of the relationship is another. The engagement model defines the partnership and impacts everything from budgeting to the level of support you receive. The goal is to find a model that solves current problems while supporting long-term objectives.
Most businesses seek to move away from the unpredictable, reactive cycle of IT support. Paying by the hour for emergency fixes is costly and does nothing to prevent future incidents. Modern engagement models are designed for stability, proactive management, and clear financial oversight.
Project-Based Engagements
A project-based model is ideal for a specific, one-time goal with a defined scope and timeline. This approach is well-suited for initiatives like a comprehensive risk assessment, a penetration test, or preparing for a compliance audit.
A consultant is engaged to complete a specific job. Once the deliverables are met, the project concludes. This model works well for businesses needing to address a particular gap or achieve a security milestone without a long-term contract.
Retainer-Based Advisory
For businesses that require ongoing strategic guidance but lack a full-time security team, a retainer-based model is an excellent middle ground. You pay a fixed monthly fee for access to an expert security advisor.
This service focuses on high-level strategy rather than hands-on technical fixes. Your consultant might help vet a new vendor’s security, develop a long-term security roadmap, or brief executives on emerging threats. It provides the benefits of a fractional CISO who keeps your security strategy aligned with your business.
Managed Security Services
The most comprehensive and proactive model is Managed Security Services. In this true partnership, the consulting firm acts as your dedicated security department for a predictable monthly fee. It bundles technology, expertise, and day-to-day management into a single subscription.
This all-in-one approach typically covers services like 24/7 threat monitoring through Managed Detection and Response, vulnerability management, and compliance reporting. It is designed for businesses that want to delegate the entire security function to a trusted partner, ensuring proactive defense and operational resilience with a fixed cost for easier budgeting.
The primary benefit of a fixed-fee managed services model is the alignment of incentives. The consultant is motivated to prevent problems, not to profit from them. This transforms the relationship from a reactive, break-fix model to a proactive partnership focused on stability.
This shift toward structured partnerships is a clear market trend. In the Caribbean, the professional cybersecurity services market is projected to reach US$144.34 million in revenue by 2025. This growth reflects how businesses in critical sectors are investing in comprehensive services to build trust and ensure operational continuity. You can dig into more of the market growth data on Statista.
What to Expect in Your First 180 Days with a Security Consultant
Engaging a cyber security consultant is a significant step, and it is important to understand what happens after the contract is signed. A well-structured engagement transforms abstract security goals into a tangible roadmap with clear, measurable milestones.
The first six months are foundational, moving from discovery and assessment to proactive defense and long-term strategic planning. This phased approach ensures the most urgent risks are addressed first while methodically building a sustainable security program.
Phase 1: Days 1–30 — Discovery and Assessment
The first month is dedicated to understanding your business. The focus is on listening and learning about your technology, operational workflows, regulatory challenges, and most valuable data.
Typical activities include:
- Initial Consultations: Meetings with leadership and key staff to map business processes, identify critical systems, and understand your primary concerns.
- Technical Discovery: A thorough review of your existing infrastructure, including network configurations, cloud environments, and current security tools.
- Vulnerability Identification: Non-intrusive scans and assessments to identify immediate, high-risk security gaps.
The primary deliverable of this phase is a comprehensive risk assessment report. This document translates technical findings into clear business terms, prioritizing risks based on their potential impact.
Phase 2: Days 31–90 — Foundational Hardening
With a clear understanding of your risk profile, the next 60 days focus on implementation. We begin deploying essential security controls to close the most critical gaps identified during the assessment. The goal is to make immediate, high-impact improvements to reduce your attack surface.
This phase typically involves:
- Implementing Essential Controls: Rolling out foundational security measures such as multi-factor authentication (MFA), advanced email filtering, and endpoint protection.
- Deploying Monitoring Tools: Setting up and configuring systems for Managed Detection and Response (MDR) to provide 24/7 visibility into network activity.
- Initial Policy Development: Drafting core security policies that establish clear rules for data handling, access control, and acceptable technology use.
By the end of this phase, your organization will have a much stronger defensive posture, with major security vulnerabilities addressed and continuous monitoring in place.
Phase 3: Days 91–180 — Strategy and Optimization
Once foundational controls are in place, the focus shifts to long-term resilience. This final phase involves building a sustainable security program that can adapt to new threats and support your business goals.
The ultimate goal of a consulting partnership is not just to implement tools, but to cultivate a security-aware culture. This phase solidifies the policies and procedures that make security an integral part of your daily operations.
Activities include refining security policies, developing a formal risk management process, and establishing clear compliance reporting. We will also create crucial documentation, such as an incident response plan template, so your team knows exactly how to act during a crisis. This forward-looking work ensures your security investment delivers lasting value.
Sample 180-Day Engagement Roadmap
| Phase | Timeline | Key Activities | Expected Outcome |
|---|---|---|---|
| Discovery | Days 1–30 | Technical review, leadership interviews, vulnerability scans | A comprehensive risk assessment report with prioritized recommendations |
| Hardening | Days 31–90 | Deploy MFA, endpoint protection, and 24/7 MDR monitoring | Critical vulnerabilities closed and real-time threat detection established |
| Strategy | Days 91–180 | Policy refinement, incident response planning, compliance reporting | A sustainable security program and a clear roadmap for the future |
This structured approach ensures that by the end of six months, you have transitioned from a reactive stance to a proactive one, with the foundation, tools, and strategy needed to protect your business.
Measuring the Business Impact of Your Investment
Investing in cyber security consulting should deliver measurable business outcomes. The objective is to connect every security effort directly to your company’s stability, financial health, and growth potential. Measuring this return on investment (ROI) requires focusing on metrics that matter to your leadership team.
Success is not just about avoiding a crisis; it is about building a more resilient, efficient, and trustworthy operation. By tracking the right metrics, you can clearly demonstrate how a proactive security strategy adds tangible value.
This timeline illustrates how a consultant methodically assesses, hardens, and strategizes your security posture, creating a clear path to measurable results.
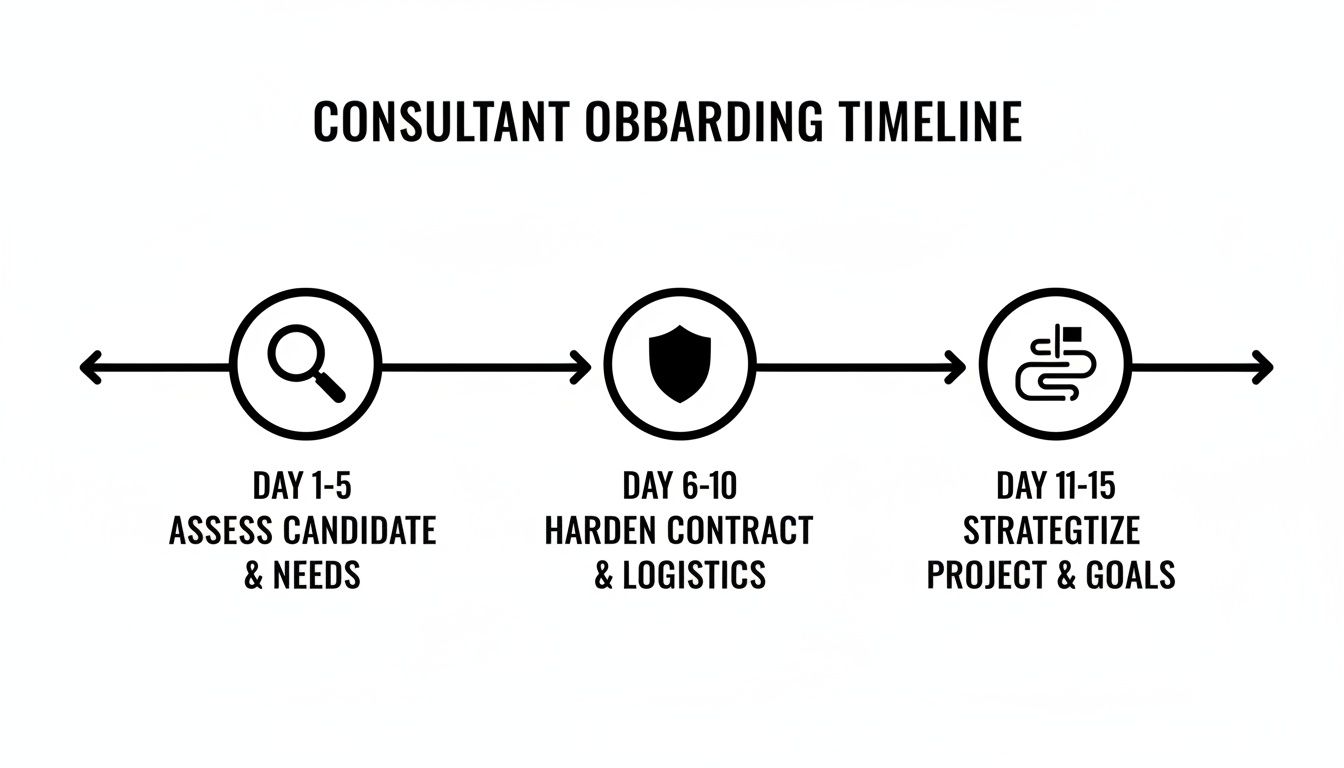
This step-by-step approach ensures every action is deliberate, moving from a deep understanding of your current state to strategic, long-term improvements.
Key Performance Indicators for Security Success
To build a strong business case for your security investment, track metrics that directly reflect lower risk and smoother operations. These KPIs provide proof that your investment is effective.
- Reduction in Security Incidents: The most direct measure of success. Track the number and severity of security alerts and verified incidents over time. A consistent decrease indicates that proactive defenses are working.
- Faster Mean Time to Respond (MTTR): How quickly can your team or partner neutralize a threat once it is detected? Reducing this time from hours or days to minutes significantly limits the potential damage from an attack.
- Improved Compliance Audit Scores: For businesses in regulated industries, passing audits is essential. Track your scores from one audit to the next; improvement demonstrates a maturing compliance and governance program.
- Decreased Security-Related Downtime: Unplanned downtime impacts revenue and reputation. Measuring the reduction in system outages caused by security issues provides a direct link between your security investment and business continuity.
The Crucial Qualitative Benefits
Beyond quantitative data, a strong security posture delivers qualitative benefits that are critical for long-term success. While harder to assign a specific dollar value, these outcomes are often what clients and partners value most.
A strong security program is a powerful business enabler. It provides the confidence needed to adopt new technologies, enter new markets, and build deeper trust with clients, knowing your critical assets are protected.
These vital, intangible benefits include:
- Enhanced Client Confidence: Demonstrating a serious commitment to security can be a significant market differentiator. Clients are more likely to choose and remain with a partner they trust to protect their sensitive data.
- Stronger Brand Reputation: A single data breach can cause lasting harm to your brand. A proactive security posture helps protect the reputation you have worked hard to build.
- Empowered Digital Innovation: A solid security foundation allows your organization to pursue growth initiatives with greater confidence. Whether adopting cloud services or new collaboration tools, you can innovate without introducing unacceptable risk.
By focusing on these business-centric outcomes, you can effectively measure and communicate the true value of your cyber security consulting partnership.
Have Questions About Cyber Security Consulting?
It is natural for business leaders to have questions when considering a security partner. Here are straightforward answers to some of the most common inquiries we receive.
How Much Does This Cost for a Small Business?
The cost of cyber security consulting for small and mid-sized businesses has become more predictable with the adoption of fixed-fee models. Instead of paying unpredictable hourly rates for emergency fixes, you invest a consistent monthly amount for proactive services like managed detection and response or vCISO guidance. This approach makes top-tier security accessible and transforms security into a manageable operational expense rather than a volatile financial risk.
Are We Too Small to Be a Target?
This is a dangerous misconception. Cybercriminals often view small and mid-sized businesses as ideal targets because they assume these companies lack robust defenses. Attackers use automated tools to scan thousands of businesses for vulnerabilities, regardless of size. Your client data, financial records, and operational continuity are valuable assets. A proactive defense is a necessity for every business, not just large enterprises.
What's the Difference Between Our IT Provider and a Security Consultant?
Your IT provider is essential for keeping daily operations running smoothly, focusing on uptime, performance, and user support. They build and maintain your IT infrastructure.
A cyber security consultant has a distinct and specialized mission: to identify and mitigate risks before they cause harm.
Consider this analogy:
- Your IT Provider is the general contractor who builds the house and ensures the utilities work.
- A Security Consultant is the structural engineer and inspector who identifies hidden weaknesses, reinforces the foundation, and installs a monitored alarm system to prevent break-ins.
While their roles may overlap, a consultant brings a dedicated focus on threat hunting, compliance, and strategic risk management that extends beyond general IT support. They are specialists focused entirely on protecting your business from sophisticated threats.
Protecting your organization requires more than just technology; it requires a proactive, strategic partner who understands your business. Tricord I.T Solutions provides expert cyber security consulting and managed services designed to build resilience and provide peace of mind.
To discuss your specific security needs, contact us for a consultation.

