A security incident response plan (IRP) is a strategic playbook that guides your business through a cybersecurity breach. Its purpose is to shift your team from a reactive, chaotic state to a calm, controlled response during a crisis. This guide provides a practical security incident response plan template to help you minimize business disruption, financial loss, and reputational damage.
An effective plan removes guesswork during a high-stress event. It pre-assigns roles, establishes clear communication channels, and maps out the exact steps needed to contain a threat and restore normal operations, ensuring a measured and defensible response.
Why an Incident Response Plan is a Business Necessity
When a cyberattack occurs, the first few hours are critical. Without a clear plan, teams scramble, crucial evidence is lost, and the damage to your business deepens with every passing minute. A well-defined IRP is a strategic tool designed to protect your company’s reputation, maintain operational continuity, and reduce financial impact.
The plan’s primary function is to provide a structured approach for managing a crisis. By defining roles and outlining procedures beforehand, you ensure a coordinated effort to contain the threat and recover systems efficiently. This preparedness is also essential for demonstrating due diligence to clients, partners, and regulatory bodies.
Key Components of an Effective IRP
A robust IRP brings clarity and direction when you need it most. While plans should be tailored to your specific business, every strong framework is built on a few foundational components. To see these concepts applied in a specific industry, consider this Incident Response Plan for Legal Aid Organizations.
Here are the primary components every IRP should include:
- Defined Roles and Responsibilities: Clearly identify who is in charge (the Incident Commander), who manages the technical response, and who handles communications. This prevents confusion and enables decisive action.
- Incident Classification System: Not all incidents carry the same risk. A system to triage issues based on severity allows you to prioritize the response according to potential business impact.
- Containment and Eradication Procedures: This is your technical action plan. It must include concrete steps to isolate affected systems, prevent the threat from spreading, and remove it from your environment completely.
- Communication Protocols: Prepare pre-approved templates and designate communication channels for notifying internal teams, clients, legal counsel, and regulatory authorities. This ensures consistent and accurate messaging.
An effective incident response plan transforms a potential catastrophe into a manageable business problem. It is the playbook that ensures a measured, efficient, and defensible response to any security event.
Ultimately, a tested IRP is the mark of a resilient organization. It signals to your team and customers that you are prepared to handle a crisis with professionalism and control. This document provides the structure you need to build that resilience. To further strengthen your defenses, explore our guide on building an advanced cybersecurity framework.
Building Your Incident Response Team
An incident response plan is only as effective as the team responsible for executing it. During a crisis, confusion over roles can lead to costly delays and critical errors. The most important step in preparing your plan is to build a dedicated Incident Response Team (IRT) with clearly defined responsibilities.
A cybersecurity incident affects more than just the IT department; it impacts finance, legal, operations, and client relations. A well-structured team ensures that every part of the business is represented and prepared to act, preventing fragmented communication and a chaotic recovery.
Defining Core Incident Response Roles
To eliminate confusion when pressure is high, every incident requires a clear chain of command. Think of it like a fire drill—everyone knows their station and responsibilities long before an alarm sounds. Specific duties must be assigned to ensure a coordinated response.
The most effective teams are built around three core functions, ensuring technical, command, and communication needs are met without overlap or gaps.
- Incident Commander (IC): This is the central decision-maker who leads the entire response. The IC is typically a strong operational leader with the authority to approve actions, assign resources, and guide the overall strategy. Their job is to coordinate the team, not perform the hands-on technical remediation.
- Technical Lead: This individual or team is responsible for the hands-on investigation, containment, and eradication. They assess the extent of the damage, isolate the threat, remove it from the network, and safely restore systems. This role demands deep technical expertise and often works closely with a managed cybersecurity partner who can provide specialized tools and experience.
- Communications Liaison: This role manages all internal and external messaging. They are responsible for coordinating with legal counsel, notifying clients, updating leadership, and ensuring all statements are consistent, accurate, and compliant. This function is vital for managing your brand’s reputation and meeting legal disclosure requirements.
The Importance of Backups and Authority
A common mistake is failing to designate backups for these critical roles. If your only Incident Commander is unavailable when an attack occurs, the entire response can stall. Every primary role needs at least one trained alternate who is ready to step in immediately.
Assigning roles isn't a one-time task. It requires regular training and practice. A team that has never worked together before will not perform effectively under the immense pressure of a live security breach.
Consider a real-world scenario: a ransomware attack compromises a server containing sensitive client data. The Incident Commander immediately convenes the IRT and authorizes the Technical Lead to isolate the infected server, preventing the malware from spreading. Simultaneously, the Communications Liaison consults with legal counsel to determine breach notification obligations while drafting a holding statement for clients.
This clear division of labor turns a potential catastrophe into a structured, manageable process. By establishing these roles before a crisis occurs, you make preparation your most powerful defense.
A Practical Framework For Incident Response
Responding to a security incident without a defined process is like navigating a storm without a compass. When an incident occurs, you need a methodical approach to regain control. An incident response lifecycle provides a predictable workflow that removes guesswork and empowers your team to act decisively.
The most widely adopted framework, established by the National Institute of Standards and Technology (NIST), breaks the response into six distinct phases. Each phase has a clear business objective, ensuring your technical actions align with organizational priorities. This structure brings clarity, reduces panic, and ensures no critical steps are missed.
The diagram below illustrates how key roles on the response team collaborate. The Commander directs the effort, coordinating the technical and communications specialists.
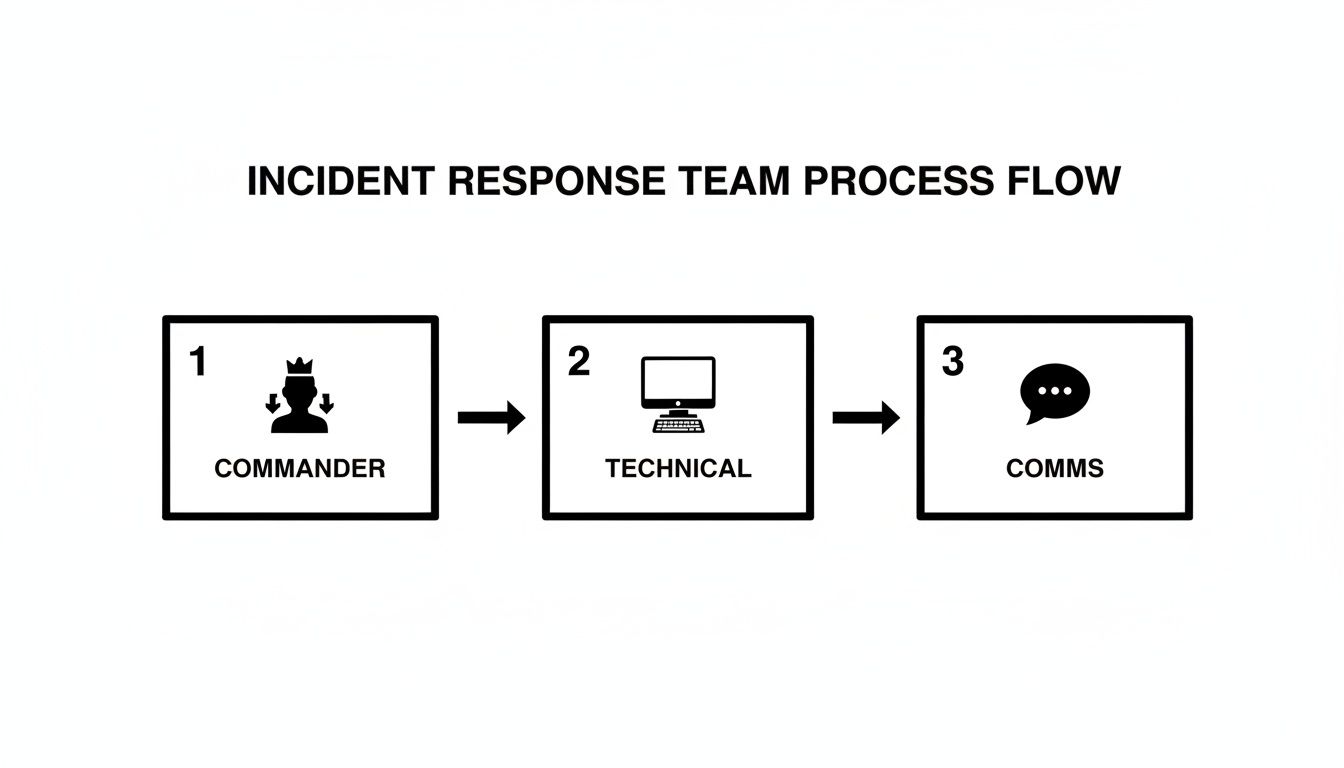
A defined process flow is essential. It emphasizes the need for centralized leadership to prevent teams from working in silos and making uncoordinated decisions during a crisis.
Here is an overview of the six phases of incident response.
| Phase | Primary Business Goal | Key Action |
|---|---|---|
| Preparation | Build resilience and readiness before an incident occurs. | Develop the plan, train the team, and deploy security tools. |
| Identification | Detect and validate a potential security incident. | Analyze alerts and system data to confirm a breach. |
| Containment | Limit the immediate impact and spread of the incident. | Isolate affected systems and block malicious activity. |
| Eradication | Completely remove the threat from the environment. | Eliminate malware, patch vulnerabilities, and reset credentials. |
| Recovery | Safely restore systems and normal business operations. | Restore data from clean backups and monitor for stability. |
| Lessons Learned | Improve future responses by analyzing the incident. | Conduct a post-mortem and update security controls and plans. |
Let's examine what each phase involves in practice.
Preparation: The Foundation Of Resilience
Preparation is the most critical phase and the one most often overlooked. This is where you do the foundational work that makes an effective response possible. It involves creating and maintaining your incident response plan, assembling your team, and ensuring everyone understands their role.
This stage is also when you implement and configure security tools, such as endpoint detection, firewalls, and logging systems. The goal is to establish a baseline of normal activity so that anomalies are easily identified. Strong preparation can transform a potential catastrophe into a manageable business problem.
Identification: Recognizing The Threat
The Identification phase begins the moment a potential incident is detected. The primary goal is to determine whether a genuine security event has occurred and, if so, to understand its scope and severity. This involves analyzing data from multiple sources, such as network alerts, unusual login patterns, or employee reports. For example, a sudden spike in outbound network traffic from a server could indicate data exfiltration.
Containment: Limiting The Damage
Once an incident is confirmed, the immediate priority is to contain it. The objective is to stop the threat from spreading and causing further damage to systems and data. The specific containment strategy will depend on the nature of the attack.
A critical business decision during containment is whether to take affected systems offline. This can stop an attack but may also halt business operations. Your IRP must clearly define who has the authority to make this decision.
Containment actions may include isolating a compromised device from the network, blocking a malicious IP address at the firewall, or disabling compromised user accounts. The key is to act quickly to cut off the attacker's access.
Eradication: Removing The Threat Completely
After containing the incident, the Eradication phase focuses on removing the threat from your environment entirely. It is not enough to stop the immediate damage; you must identify and address the root cause to prevent recurrence.
This could involve removing malware, patching the vulnerabilities that were exploited, and resetting all compromised credentials. It is a methodical process designed to ensure no trace of the attacker remains. You can learn more about building a solid defense by exploring our guide on advanced cybersecurity frameworks.
Recovery: Restoring Normal Operations
With the threat eliminated, the Recovery phase focuses on safely restoring systems and data to normal operations. This process must be handled carefully to avoid re-introducing a vulnerability. It typically involves restoring data from verified clean backups, closely monitoring systems for any signs of compromise, and obtaining formal confirmation that operations are secure.
Lessons Learned: Strengthening Future Defences
The final phase, Lessons Learned, is as important as the first. It involves a post-incident review to analyze what happened, how the team responded, and what could be improved. This should be a blameless post-mortem focused solely on strengthening security controls and processes.
The outcome should be an updated incident response plan, improved procedures, and potentially a business case for new security investments. As you build your framework, remember the importance of documenting every incident; learn more about crafting effective security incident reports. This cycle of continuous improvement turns every incident into an opportunity to become more resilient.
Making the Plan Your Own
A template is a starting point, not a complete solution. To be effective, a security incident response plan must be customized to the unique technologies, risks, and compliance requirements of your business. Simply downloading a template without tailoring it is like using a generic map for a specific journey—it provides general direction but misses the critical details needed for success.
The objective is to transform a theoretical document into a practical playbook your team can use under pressure. This means defining what constitutes an "incident" for your business, establishing communication channels, and aligning procedures with the tools you use daily, such as those in the Microsoft 365 ecosystem.
Define What an "Incident" Really Means for You
Not every security alert is a crisis. A single blocked phishing email is vastly different from a ransomware attack that encrypts your client database. Your plan needs a clear classification system so your team can focus its resources on events with the greatest business impact.
Create a simple matrix to define severity levels (e.g., Low, Medium, High, Critical) based on key business-focused questions:
- Data Impact: Is sensitive client, financial, or employee data at risk?
- Operational Disruption: Are core business operations or client services interrupted?
- Reputational Damage: Could this incident erode client trust or harm our brand?
- Legal and Compliance Risk: Does this event trigger mandatory notification requirements?
This framework provides your Incident Commander with the clarity needed to allocate resources effectively, ensuring the most significant threats receive immediate attention.
Nail Down Your Communication Protocols
During a crisis, inconsistent or confusing messaging can cause more damage than the incident itself. Your plan must specify who communicates with whom, what they say, and when. This requires developing distinct communication plans for different audiences.
Internal messages to employees will focus on procedures and maintaining operational stability. Client notifications, which must be reviewed by legal counsel, need to be factual, empathetic, and compliant. Updates for partners or regulators will have their own specific requirements for tone and content.
A well-defined communication strategy is not developed on the fly; it is a fundamental component of damage control. Having pre-drafted templates for key scenarios prevents panicked, ad-hoc messages that can worsen a difficult situation.
The need for clear protocols is evident. Recent regional cyber incidents underscore the need for prepared response plans, as breaches have impacted businesses across various sectors, often exposing sensitive consumer data due to security gaps.
Align the Plan with Your Tech and Compliance Needs
Finally, your response plan must be grounded in your specific technology stack and regulatory environment. If your business relies on SharePoint for document management, your containment and recovery steps must include specific actions for securing SharePoint sites and restoring data. The plan must reference your actual systems, not generic placeholders.
Compliance is another non-negotiable factor. A law firm's breach notification duties differ significantly from a healthcare provider's obligations under HIPAA or PIPEDA. Your plan must integrate these industry-specific requirements, detailing every step needed to meet legal obligations, including strict reporting deadlines. This alignment ensures your response is not only technically sound but also legally defensible.
Testing And Maintaining Your Response Plan
An incident response plan that is not regularly tested is a liability. It creates a false sense of security, leaving your organization unprepared for a real crisis. An IRP is a living document that must be tested, refined, and updated regularly to remain effective against evolving cyber threats.
If you don't test your plan, you won't discover its weaknesses until you are in the middle of an actual incident—the worst possible time to find flaws.
Get Real with Tabletop Exercises
The most effective way to validate your plan is through a tabletop exercise. This is a simulated cyberattack drill where your Incident Response Team gathers to walk through a realistic scenario in a controlled environment. The goal is not to pass a test but to identify weaknesses, unclear instructions, and procedural gaps before a crisis occurs.

A valuable tabletop exercise feels real. The scenario should be plausible for your organization and industry, forcing the team to use the specific procedures outlined in the plan.
For example, a law firm might simulate a business email compromise (BEC) attack where an attacker impersonates a partner to authorize a fraudulent wire transfer. This scenario tests your identification, containment, and communication protocols.
A facilitator guides the team through the incident, asking pointed questions at each stage:
- Identification: "The finance team has flagged a suspicious wire transfer. According to the plan, who is notified first?"
- Containment: "What are the immediate steps to verify the request and stop the transfer? Who has the authority to cancel the transaction?"
- Communication: "How do we inform leadership? What does our client communication plan require in this situation?"
This process reveals where the plan is strong and where it needs improvement.
The most crucial part of a tabletop exercise is the honest debrief that follows. It should be a blameless forum to ask: "Where did we hesitate? Was any part of the plan unclear? Did everyone know their role?" This feedback is invaluable for strengthening your response.
Set a Schedule for Reviews and Updates
Testing is not a one-time event. Your IRP must evolve with your business. A plan written last year may already be outdated due to new technologies, personnel changes, or updated compliance requirements.
Establish a formal review and maintenance cycle to keep your plan relevant and useful.
Consider this practical cadence for maintaining your plan:
- Annual Tabletop Exercise: Conduct a full simulation at least once a year to test the entire plan and provide hands-on team training.
- Quarterly Plan Review: The Incident Commander and key stakeholders should meet quarterly to review the document and incorporate updates based on minor organizational changes.
- Post-Incident Updates: After any real security incident, hold a "lessons learned" session and immediately update the plan with your findings.
- Trigger-Based Reviews: Major business changes, such as mergers, new office locations, or a significant cloud migration, should automatically trigger a full plan review.
This disciplined approach ensures your plan remains an operational tool you can rely on. Public sector bodies like those described in reports on California's cybersecurity activities inform effective response planning, constantly refine their frameworks, offering a sound model for private businesses.
By committing to regular testing and maintenance, you transform your security incident response plan template from a static document into a dynamic defense. This proactive approach is closely linked to overall business continuity, a topic covered in our guide to IT disaster recovery plan templates.
What To Do Next
You now have the framework for a solid security incident response plan, but a template is only the beginning. The real work involves shifting from a mindset of reactive damage control to one of proactive, intelligent defense. This plan should be the catalyst for a broader evaluation of your entire security posture.
An effective response plan is only one part of a comprehensive strategy. The ultimate goal is to prevent incidents from occurring in the first place, which requires a clear understanding of your current vulnerabilities and operational risks.
From Planning to Proactive Defence
It is time to translate this planning exercise into tangible security improvements. A generic template is a start, but a plan tailored to your business and integrated with proactive security measures is what will truly protect you from financial loss and reputational harm. The goal is to build a security foundation so strong that you rarely need to use your incident response plan.
An incident response plan manages a crisis already in progress. A proactive cybersecurity strategy aims to prevent that crisis from ever happening. Your business needs both for long-term resilience.
Take Action with an Expert Partner
We encourage you to use this template to initiate a more strategic conversation about your security. Engaging an expert partner can provide the external perspective and deep technical knowledge needed to move forward with confidence.
A comprehensive approach includes several key steps:
- Conducting a Security Assessment: Identify and prioritize vulnerabilities across your entire technology environment, from on-premises hardware to cloud applications.
- Tailoring Your IRP: Customize this security incident response plan template to align with your operational procedures, compliance requirements, and specific business risks.
- Implementing Managed Defences: Deploy managed cybersecurity services designed to detect and neutralize threats before they can cause significant damage.
Taking these steps transforms your plan from a static document into a dynamic component of a resilient business strategy. To understand how this fits into the broader context of organizational resilience, read our article on the fundamentals of business continuity planning.
Frequently Asked Questions
When it comes to incident response, business leaders often ask similar questions about testing, common pitfalls, and working with an IT partner. Here are clear answers based on our experience.
How Often Should We Test Our Security Incident Response Plan?
At a minimum, you should conduct a formal tabletop exercise annually. This simulation is the most effective way to identify gaps in your plan within a low-pressure environment before a real crisis occurs.
However, the annual test is just the baseline. You should also review the plan whenever your organization undergoes significant changes, such as adopting a new cloud platform, experiencing turnover in key response roles, or acquiring another company. The threat landscape is constantly evolving, so regular testing keeps your team prepared and your plan relevant.
What Is The Biggest Mistake Businesses Make With Incident Response?
The most common and costly mistake is creating a plan that is never tested or updated. An outdated plan provides a false sense of security and is likely to fail when needed most, leading to a chaotic response and unnecessary delays.
A close second is mismanaging communications. Without a predefined and practiced communication strategy for employees, clients, and legal counsel, a manageable incident can quickly become a reputational crisis. Unclear or panicked messaging erodes trust and can increase business liability.
A plan is only valuable if it’s a living document. The goal isn't just to have a plan, but to cultivate a team that has the muscle memory to execute it calmly and effectively under pressure.
Does A Managed IT Partner Replace The Need For Our Own Plan?
No. A managed IT and cybersecurity partner is a crucial component of your plan, but they do not replace it. They act as your technical specialists, handling the hands-on work of containment, eradication, and recovery.
Your internal plan governs the critical business decisions that only you can make. It must answer questions such as:
- Who has the authority to declare a security incident?
- Who is responsible for communicating with clients, stakeholders, and staff?
- Who can authorize expenses related to the response and recovery?
Your plan defines your organization's roles, responsibilities, and decision-making authority. Your managed services provider executes the technical strategy within that framework. The two work together to ensure a seamless and comprehensive response.
A well-crafted security incident response plan is a strategic asset. At Tricord I.T Solutions, we help organizations move from planning to building a proactive defense by tailoring response plans and implementing managed cybersecurity services designed to stop incidents before they happen. Schedule a consultation to strengthen your security posture.

