Endpoint Detection and Response (EDR) is a cybersecurity technology that continuously monitors company devices—such as laptops, servers, and computers—to detect and stop advanced threats. Unlike traditional antivirus software that primarily blocks known malware, EDR actively looks for suspicious behavior. This proactive approach allows it to neutralize sophisticated cyberattacks before they can cause significant business disruption or financial loss.
For business leaders, EDR provides a critical layer of defense against modern threats like ransomware and data breaches. By offering deep visibility into endpoint activity, it enables rapid containment of security incidents, reducing operational risk and helping to meet compliance requirements.
Why Traditional Antivirus Is No Longer Enough
Think of traditional antivirus software as a security guard with a list of known troublemakers. If someone on the list tries to enter, they are blocked. This system is effective against common, previously identified threats but is easily bypassed by new or custom-designed attacks that aren't on the list. Modern cybercriminals specialize in creating threats designed to walk right past this basic defense, leaving your business exposed.
This is where Endpoint Detection and Response provides a necessary evolution. EDR acts less like a guard at the door and more like a modern surveillance team monitoring activity across the entire facility. It doesn't just look for known threats; it analyzes behavior to identify actions that are out of the ordinary.
For example, if an employee's accounting software suddenly attempts to encrypt thousands of files on a shared server, that is abnormal behavior. An EDR system flags this activity, even without a known virus signature, and can automatically isolate the device to stop a potential ransomware attack in its tracks.
Endpoints are a primary target for attackers. In Canada, for example, compromised endpoints are a leading cause of security incidents. To understand the scale of the issue, you can learn more about the rise of endpoint attacks from recent market analysis. EDR is an essential tool for mitigating this risk.
Core Functions of an EDR Solution
To understand what endpoint detection and response means for your business, it is helpful to review its four key functions. Each step is critical for protecting your organization from a data breach or operational shutdown.
The table below outlines these core functions from a business perspective, showing how each stage contributes to a more resilient security posture.
| Function | Description for Business Leaders |
|---|---|
| Monitor | Continuously collects activity data from all company devices (endpoints), establishing a baseline of normal operations. |
| Detect | Uses advanced analytics and threat intelligence to identify suspicious patterns and behaviors that deviate from the established norm. |
| Investigate | Provides security analysts with the contextual data and tools needed to quickly determine the origin and scope of a potential threat. |
| Respond | Automatically contains threats by isolating the affected endpoint or terminating the malicious process to prevent further damage. |
In short, an EDR solution provides the visibility to see what is happening on your network and the power to stop threats before they escalate. It is a proactive defense designed for today’s complex cyber threat landscape.
How EDR Works in a Real-World Scenario
To illustrate the practical value of EDR, let's consider a scenario involving a professional services firm, where protecting confidential client information is a core business requirement.
An employee receives a sophisticated phishing email that appears to be from a trusted partner. They click a link, which executes a malicious script on their laptop. Without EDR, this script could operate undetected for days, quietly mapping the network and preparing to encrypt files on the firm’s document server or within its Microsoft 365 environment.
The Automated Security Workflow
Now, let’s replay the scenario with an EDR solution in place. The outcome is entirely different.
An EDR agent runs silently on the laptop, continuously monitoring all system processes. The moment the script begins its malicious activity—such as a common application attempting to encrypt files at high speed—the EDR agent detects the abnormal behavior. This is a classic indicator of a ransomware attack.
The EDR platform’s automated response capabilities activate immediately:
- Isolate: The infected laptop is instantly disconnected from the company network, cutting off access to shared drives and cloud services.
- Terminate: The malicious process is stopped before it can cause widespread damage.
- Alert: The IT team or managed security provider receives a detailed notification explaining the incident, the affected device, and the automated actions taken.
This automated workflow transforms a potential crisis into a contained, manageable event.
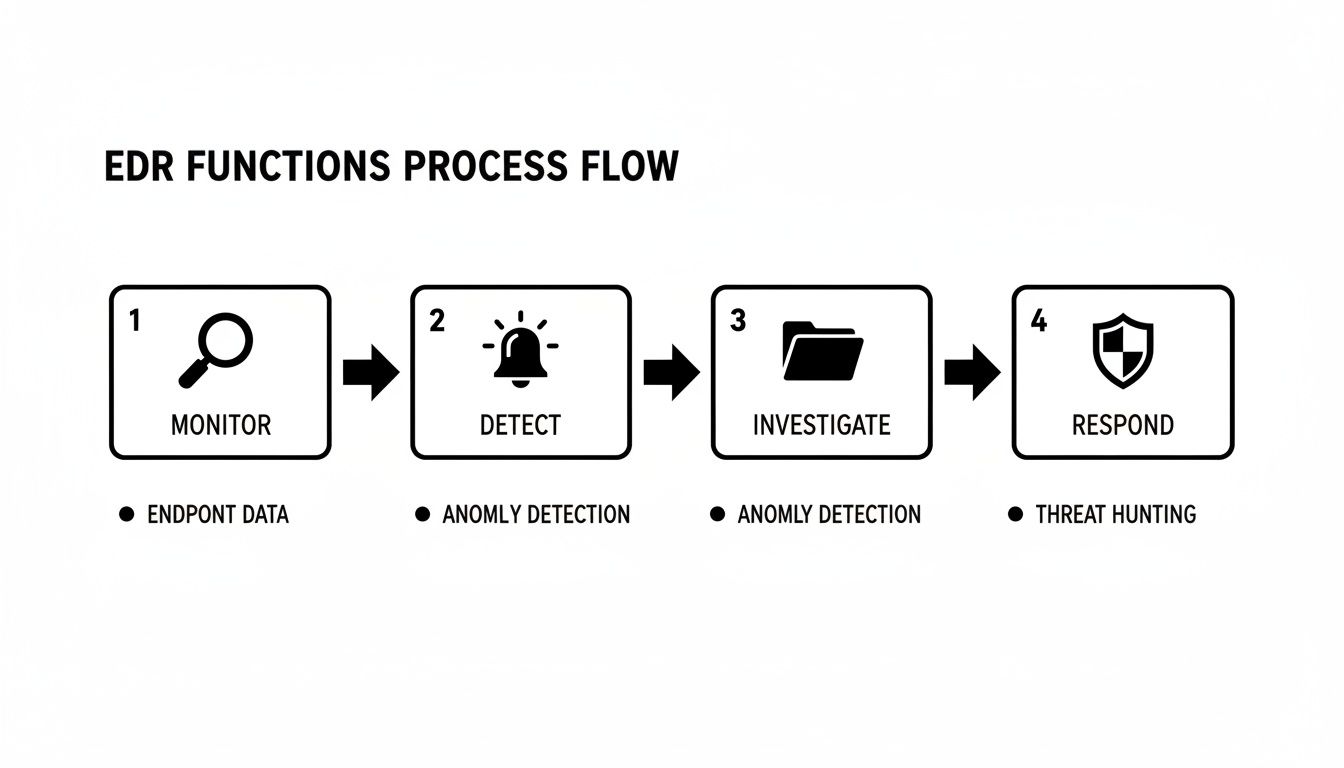
This cycle—Monitor, Detect, Investigate, and Respond—is the engine that makes EDR a powerful defense. It is what contains threats before they can spread across the organization.
In this scenario, what could have been a catastrophic data breach becomes a non-event. The threat is neutralized in seconds, preventing operational disruption, financial loss, and reputational damage.
From Containment to Resolution
After the immediate threat is contained, the security team uses the rich data collected by the EDR tool to investigate the root cause of the incident and ensure all traces of the threat are removed.
This proactive response cycle is the foundation of modern cybersecurity. For firms looking to formalize their procedures, our incident response plan template provides a structured framework for managing security events. The speed and precision of EDR highlight its ultimate business value: minimizing risk and ensuring operational continuity.
Comparing EDR, Antivirus, and XDR
When evaluating cybersecurity tools, it is easy to get lost in acronyms. Understanding the differences between Antivirus (AV), Endpoint Detection and Response (EDR), and Extended Detection and Response (XDR) is critical for making an informed investment. While they may sound similar, they address different levels of risk.
Traditional antivirus is a reactive tool. It stands at the door, blocking known threats by matching their digital "signatures." While a necessary first line of defense, it is blind to modern, custom-built malware or fileless attacks that have no existing signature.
This limitation is why businesses are upgrading their defenses. Organizations recognize that relying solely on antivirus is no longer sufficient. If you are interested in broader market trends, you can find additional research on cybersecurity spending from market data forecasts.
EDR: The Proactive Investigator
Endpoint Detection and Response is a significant step forward. Instead of only checking for known threats, EDR proactively monitors the behavior occurring on your devices. It looks for suspicious patterns of activity that indicate an attack is in progress, even if the malware itself is new.
If antivirus is the security guard at the front door, EDR is the surveillance team monitoring activity inside the building, ready to neutralize a threat before it can cause serious harm. It provides the deep visibility needed to investigate and stop sophisticated attacks.
XDR: The Holistic Correlator
Extended Detection and Response (XDR) expands this surveillance network even further. It does not just monitor endpoints; it aggregates and correlates security data from your entire IT environment, including email systems, cloud applications like Microsoft 365, and network devices.
By connecting events from these different sources, XDR provides a single, unified view of a complex attack. For example, it can trace a threat that began with a phishing email, moved to a laptop, and is now attempting to access files in the cloud. This 360-degree visibility is powerful but is often best suited for larger enterprises with dedicated security operations teams.
The table below clarifies how each solution compares.
Comparison of Antivirus, EDR, and XDR
| Capability | Traditional Antivirus (AV) | Endpoint Detection and Response (EDR) | Extended Detection and Response (XDR) |
|---|---|---|---|
| Primary Focus | Blocking known viruses and malware. | Detecting and responding to suspicious activity on endpoints. | Correlating security data across the entire IT environment. |
| Detection Method | Signature-based (matches known threats). | Behavior-based (identifies anomalous activity). | Cross-domain analytics (connects alerts from all sources). |
| Business Purpose | Foundational device protection. | Proactive threat containment and investigation. | Comprehensive visibility for advanced threat hunting. |
For most small and midsize businesses, EDR offers the right balance of advanced protection and manageable complexity. It secures your most vulnerable assets—your endpoints—providing a strong foundation for a resilient and compliant security posture. Our approach to cybersecurity solutions focuses on implementing right-sized tools for your specific risk profile, ensuring you are protected where it matters most.
The Business Benefits of Implementing EDR
While the technical capabilities of Endpoint Detection and Response (EDR) are impressive, its true value is measured in business outcomes. Implementing EDR delivers tangible benefits, including reduced risk, improved operational stability, and a stronger compliance position. For business leaders, these outcomes make EDR a strategic investment rather than just another IT expense.
At its core, EDR shifts your security posture from reactive to proactive. Instead of waiting to block known threats, it actively hunts for unusual activity, allowing you to stop an attack before it causes significant damage. This proactive stance is the foundation for several key business advantages.

Enhanced Threat Visibility and Speed
One of the most significant benefits of EDR is its ability to dramatically reduce attacker "dwell time"—the critical period when a threat actor operates undetected within your network. EDR provides deep visibility into endpoint activity, illuminating suspicious behavior that traditional antivirus would miss. This means threats are detected and neutralized faster.
The impact of this speed is clear. Organizations that use integrated EDR and identity protection solutions can reduce their mean time to detect (MTTD) from weeks to hours and cut incident containment times significantly. For a midsize business, this speed is the difference between remediating a single workstation and managing a full-scale data breach. You can review key insights on financial sector cyber resilience for more data on this topic.
Reduced Risk and Improved Resilience
By detecting threats early, EDR significantly lowers the risk of a data breach that could disrupt operations or damage your reputation. Its ability to automatically isolate an infected device is a critical feature, preventing an incident on one laptop from escalating into a company-wide crisis.
This rapid containment capability directly enhances your operational resilience, ensuring your business can continue to function during a security event. This is especially important for our managed IT services clients, who depend on consistent uptime to serve their customers.
For a regulated business like a law firm, a single compromised endpoint could lead to a breach of client confidentiality. EDR acts as a critical safeguard, preventing that initial foothold from spreading to sensitive case files stored in your document management system.
Meeting Compliance and Insurance Requirements
In today's business environment, EDR is becoming a prerequisite for organizations subject to regulatory oversight or seeking cyber insurance. Regulations like Canada's PIPEDA require businesses to demonstrate they are taking reasonable measures to protect personal information. EDR provides the detailed activity logs and incident response documentation needed to prove compliance.
Furthermore, cyber insurance carriers increasingly mandate EDR as a condition for coverage. They recognize that its advanced capabilities are essential for managing the risks they underwrite. Implementing a professionally managed EDR solution signals that you take your cybersecurity responsibilities seriously, making your business a more insurable risk.
How to Choose the Right EDR Solution
Recognizing the need for Endpoint Detection and Response (EDR) is the first step; selecting the right solution or partner is what determines its success. The key is to find a platform that aligns with your company’s operational capacity, risk tolerance, and existing technology stack.
An improper choice can lead to significant challenges, such as overwhelming an internal team with false alerts, creating security gaps due to poor integration, or incurring unexpected management costs. The goal is to implement a solution that effectively stops threats without introducing unnecessary complexity.
Key Decision Criteria
When evaluating your options, focus on practical business considerations rather than technical jargon. Use this checklist to guide discussions with potential vendors and IT partners:
- Integration with Existing Tools: Does the solution integrate seamlessly with your current systems, particularly productivity suites like Microsoft 365? A well-integrated tool provides better visibility and simplifies management, preventing your team from having to manage multiple, disconnected platforms.
- Management and Expertise Required: Who will monitor alerts and respond to threats? EDR is not a "set it and forget it" technology. It requires continuous oversight from skilled security professionals who can interpret data and act quickly.
- Degree of Response Automation: How much of the response process can be automated? Look for solutions that can automatically quarantine an infected device or terminate a threat without human intervention. This speed is critical for minimizing damage.
In-House vs. Managed EDR
A primary decision is whether to manage an EDR solution internally or partner with a managed security service provider. An in-house approach offers complete control but requires a significant investment in a 24/7 security team with specialized expertise—a resource few small and midsize businesses can afford to build and maintain.
For most organizations, a managed EDR service offers a more practical and cost-effective path to advanced security. It provides access to a dedicated team of experts who handle the monitoring, analysis, and response around the clock, allowing your team to focus on core business priorities.
Partnering with a managed provider ensures the technology is configured correctly and that every alert is investigated by experienced professionals who can distinguish a real threat from a false alarm. This approach aligns with broader strategies for building a resilient security operation, a topic we explore in our guide to advanced cybersecurity frameworks. The right choice ultimately depends on your organization's resources, risk appetite, and strategic goals.
Time to Strengthen Your Endpoint Security
Endpoint Detection and Response is no longer an optional security tool; it is a core defense for any modern business. Traditional antivirus cannot keep pace with the sophisticated threats targeting your company's most vulnerable assets—the laptops, servers, and other devices your team uses every day.
EDR provides the visibility and rapid response capabilities necessary to protect sensitive data, maintain operations during an incident, and meet growing compliance and insurance demands.
The path forward is not about adding more software, but about implementing a clear, proactive strategy that addresses your specific business risks.
Your Practical Next Steps
To build a more resilient security posture, we recommend focusing on three key actions:
-
Assess Your Current Endpoint Risk: Identify where your most critical data resides and which employees or systems have access to it. A clear understanding of your risk landscape is the foundation of an effective security strategy.
-
Review Compliance and Insurance Obligations: Examine your regulatory requirements and cyber insurance policies. Many now mandate advanced endpoint protection, and EDR often satisfies this requirement.
-
Evaluate Your Security Capabilities: A successful security strategy involves your people. Investing in their skills through structured end-user cyber awareness training can significantly reduce the likelihood of a successful phishing attack, reinforcing your technical defenses with a knowledgeable human firewall.
Adopting EDR is a significant step toward achieving a mature cybersecurity posture. If you are ready to discuss your organization's needs, our team is here to provide expert guidance and help you develop a security roadmap that aligns with your business goals.
Your EDR Questions, Answered
When business leaders consider Endpoint Detection and Response, several practical questions about its impact on day-to-day operations often arise. Here are straightforward answers to the most common inquiries we receive.
Will EDR Slow Down Our Computers?
This is a valid concern, particularly for those who have experienced performance issues with older antivirus software. Modern EDR agents are engineered to be lightweight and efficient. They operate in the background with a minimal performance footprint, allowing your team to work without frustrating slowdowns or interruptions.
We Already Use Microsoft 365 Defender. Isn't That EDR?
Yes, Microsoft Defender for Endpoint is a powerful EDR solution included in many Microsoft 365 business subscriptions. However, simply having the tool is only the first step. Its value is fully realized when it is expertly configured, monitored, and managed 24/7. An IT partner ensures that alerts are properly investigated and that the platform’s advanced features are optimized to protect your specific environment, transforming a powerful tool into a complete security solution.
Can We Just Manage EDR Ourselves?
While technically possible, effectively managing an EDR platform is a full-time responsibility that requires a dedicated security operations team. This team must possess specialized expertise to analyze a constant stream of alerts, distinguish real threats from false positives, and respond to incidents within minutes. For most businesses, partnering with a managed security provider is a more practical and cost-effective approach to achieving this level of protection.
How Much Is This Going to Cost?
EDR pricing depends on the number of devices you need to protect and the level of management you choose. It is important to weigh this investment against the potential cost of a data breach, which includes downtime, regulatory fines, and reputational damage. Managed EDR services provide this advanced protection for a predictable monthly fee, converting a significant capital investment into a manageable operational expense.
Ready to strengthen your endpoint security with a proactive, managed approach? Our team can help you assess your risk and implement the right EDR strategy for your business. Schedule a consultation with us today.