IT governance is the framework of rules, policies, and processes that ensures a company's technology strategy supports its overall business objectives. In simple terms, it's the leadership and organizational structure for making sure IT investments deliver value, manage risks effectively, and comply with legal and regulatory requirements. Without it, technology decisions can become disjointed, wasteful, and insecure.
For business leaders, IT governance provides a clear line of sight between technology spending and business outcomes. It transforms IT from a reactive cost center into a strategic asset that drives efficiency, manages risk, and supports sustainable growth. This structure is essential for aligning technology with your core business goals of profitability, resilience, and compliance.

Defining the Role of IT Governance in Your Business
Many business leaders view IT as a necessary expense to keep operations running. IT governance challenges this perspective, reframing technology as a strategic driver of business value. It provides the formal structure needed to move from chaotic, reactive IT decisions to a deliberate, forward-looking technology roadmap.
Without a governance plan, departments often make technology decisions in isolation. This leads to redundant software purchases, inconsistent security protocols, and a clear disconnect between IT spending and business results. The consequences are wasted capital, significant security vulnerabilities, and missed opportunities for innovation.
The Bridge Between Technology and Business Goals
Effective IT governance acts as the critical link between high-level business strategy and day-to-day technology operations. It establishes a formal system for accountability, ensuring that every hardware upgrade, software license, and security policy is implemented to enhance business resilience, profitability, and growth.
IT governance is a core component of the broader discipline of Governance, Risk, and Compliance (GRC). This connection highlights that its purpose is not just to manage technology assets but to protect the entire organization from digital threats, operational disruptions, and costly regulatory penalties.
Think of it this way: Your business strategy sets the destination. Your IT infrastructure is the vehicle to get there. IT governance serves as both the GPS and the driver's manual, ensuring you take the most efficient, safe, and cost-effective route.
Core Components of an IT Governance Framework
A robust governance framework is built on several key pillars that work together to provide comprehensive oversight. These components translate abstract strategies into concrete actions with measurable business outcomes. Understanding them clarifies what effective IT governance looks like in practice.
The table below breaks down the essential functions of a well-designed IT governance program.
| Pillar | Objective and Business Impact |
|---|---|
| Strategic Alignment | Ensures IT initiatives and investments directly support overarching business goals, maximizing ROI and competitive advantage. |
| Value Delivery | Focuses on optimizing IT expenses and proving the value of technology through efficiency gains, cost savings, and new revenue streams. |
| Risk Management | Identifies, assesses, and mitigates IT-related risks, including cybersecurity threats, data breaches, regulatory non-compliance, and system failures. |
| Resource Management | Guarantees the optimal allocation and use of IT assets—including infrastructure, software, and personnel—to meet business demands effectively. |
| Performance Measurement | Monitors and reports on IT performance using clear metrics (KPIs) to track project success, service quality, and overall contribution to the business. |
Each pillar plays a distinct but interconnected role, ensuring that technology doesn't just function—it performs.
Why IT Governance Is a Strategic Imperative
In today's economy, technology is no longer a back-office utility; it is the engine that powers nearly every aspect of business. This shift has elevated IT governance from a technical checklist to a critical board-level responsibility. Ignoring it introduces unacceptable levels of risk and inefficiency into the organization.
The need for formal governance is driven by three primary forces: escalating business risks, from sophisticated cyberattacks to accidental data leaks; increasing regulatory pressures, such as data privacy laws with severe financial penalties; and the complete operational reliance on technology, where any disruption directly impacts revenue and client trust.
Navigating Risk in a Digital-First World
Without a guiding framework, technology decisions often occur in silos, creating a patchwork of systems that are difficult to manage and secure. For example, a department might adopt a new cloud application without proper security vetting, inadvertently creating a new entry point for attackers. This lack of centralized oversight is a direct invitation to operational disruption and data loss.
For businesses in regulated industries like law or finance, the consequences are particularly severe. A single data breach can trigger crippling fines, mandatory public disclosures, and irreversible reputational damage. Strong governance transforms this reactive, high-risk environment into a proactive one where security and compliance are integrated into every technology decision from the outset.
Effective IT governance is not about slowing down innovation with bureaucracy. It is about enabling sustainable growth by ensuring technology decisions are sound, secure, and aligned with your most important business objectives.
Meeting Modern Compliance Demands
The regulatory landscape is becoming increasingly complex, placing a heavy burden on organizations to demonstrate responsible stewardship of sensitive information. IT governance provides the documented evidence—the policies, audit logs, and risk assessments—that proves due diligence to regulators and clients. It formalizes how you manage client data, control user access, and respond to security incidents.
In the Caribbean, rising cyber risks and new regulations have made IT governance a pressing board-level issue. A 2025 study on governance futures in Caribbean Small Island Developing States (SIDS) noted that public sectors face challenges with “lagging legal reforms, weak data governance, and rising cyber threats,” increasing the responsibility of private organizations to secure their own information systems. Discover more about how these regional trends are shaping governance expectations.
This trend makes it clear: operating without a formal governance structure is like navigating without a compliance roadmap. A costly violation becomes a matter of when, not if. A strong framework builds a resilient, competitive, and trustworthy organization capable of meeting today's challenges.
Understanding Popular IT Governance Frameworks
Implementing IT governance does not require starting from scratch. Established frameworks provide proven blueprints for building a program tailored to your business needs. These are not rigid academic theories but practical toolkits designed to bring structure, strategy, and accountability to your technology operations.
Adopting a recognized framework helps you implement best practices quickly, ensure comprehensive coverage of key risk areas, and demonstrate a credible approach to auditors, regulators, and partners. For business leaders, understanding the focus of each framework is the first step toward selecting the right one.
COBIT: The Governance and Management Framework
COBIT (Control Objectives for Information and Related Technologies) is widely regarded as the leading framework for enterprise-level IT governance. Its primary function is to bridge the common gap between technical issues, business risks, and compliance requirements. COBIT helps ensure that technology investments generate tangible value while associated risks are managed appropriately.
It provides a comprehensive set of principles and practices designed for organizational leadership. COBIT helps executives answer critical questions like, "Are we getting the best value from our IT investments?" and "Are we managing our IT-related risks effectively?"
ITIL: The Service Management Framework
While COBIT focuses on what the business needs from IT, ITIL (Information Technology Infrastructure Library) focuses on how to deliver IT services efficiently and reliably. ITIL is a set of detailed best practices for IT service management (ITSM) that aligns technology services with the day-to-day needs of the business. It is the go-to framework for standardizing processes for the IT helpdesk, system maintenance, and incident response.
Adopting ITIL helps create a more predictable and efficient operational environment. It ensures that when an employee needs technical support or a critical system fails, a clear, repeatable process is in place to resolve the issue quickly and minimize business disruption. In Germany, for example, balancing AI innovation with strategic risk, compliance, and governance management is a key challenge where ITIL's process-oriented approach can provide stability.
NIST: The Cybersecurity Framework
The NIST Cybersecurity Framework (CSF), developed by the U.S. National Institute of Standards and Technology, is the definitive standard for managing cybersecurity risk. While not a comprehensive governance framework like COBIT, it has become an essential pillar of any modern IT governance program. The NIST CSF provides a clear structure for organizations to identify, protect against, detect, respond to, and recover from cyberattacks.
Its risk-based, adaptable approach makes it suitable for businesses of all sizes, offering a clear path to improved cyber resilience. For many organizations, the NIST framework serves as the foundation for their security policies and controls. You can learn more about how to safeguard your data by exploring advanced cybersecurity frameworks.
While each framework has a different focus, they are not mutually exclusive. Many successful organizations blend elements from all three to create a comprehensive governance program tailored to their unique operational needs and risk profile.
The table below offers a high-level comparison to help simplify the differences.
| Framework | Primary Focus | Best Suited For |
|---|---|---|
| COBIT | Enterprise Governance & Risk | Aligning IT strategy with business goals and satisfying audit and compliance requirements at a leadership level. |
| ITIL | IT Service Management | Standardizing and improving the quality, efficiency, and reliability of day-to-day IT operations and user support. |
| NIST CSF | Cybersecurity Risk Management | Building a resilient and adaptable program to protect against, detect, and respond to evolving cyber threats. |
Ultimately, choosing the right framework—or combination of frameworks—depends on your organization’s priorities. Whether your primary driver is regulatory compliance, operational efficiency, or improved security, a proven blueprint exists to guide your efforts.
Applying Governance to Microsoft 365 and SharePoint

IT governance demonstrates its true value when applied to the tools your team uses every day. For most modern businesses, that means platforms like Microsoft 365 and SharePoint. Without clear rules of the road, these powerful collaboration tools can quickly become a disorganized and insecure repository of sensitive company data.
Applying governance principles here transforms these applications into a secure, compliant, and highly productive digital workspace. It is the practical application of your high-level strategy, ensuring your most critical business information is managed with intent. This is how you maximize the return on your Microsoft investment and turn it into a secure, well-managed business asset.
Establishing Control Over Your Digital Files
A primary function of governance in Microsoft 365 is managing the lifecycle of documents and data. This involves creating and enforcing clear policies for how information is created, stored, shared, and ultimately archived or deleted. Uncontrolled data growth increases storage costs, complicates legal discovery, and makes it nearly impossible for employees to find what they need.
For example, a professional services firm can use governance policies to automatically classify documents containing sensitive client information. This classification can then trigger specific retention rules, ensuring the file is kept for the legally required period and then securely disposed of, minimizing long-term risk and liability.
Key governance actions for document management include:
- Document Lifecycle Policies: Automatically archiving project files six months after a matter is closed to reduce clutter and lower storage costs.
- Data Loss Prevention (DLP): Configuring rules that block emails containing sensitive financial or client data from being sent outside the company network.
- Clear Naming Conventions: Enforcing a standard structure for file and folder names to make information discovery fast and intuitive for everyone.
Securing Access and Preventing Data Sprawl
Without governance, access permissions can quickly become a tangled mess. As employees change roles and new project teams are formed, it is easy for too many people to gain access to information they don't need. This creates significant security vulnerabilities and compliance risks, particularly in regulated industries.
Governance brings structure to access control. It begins with establishing clear ownership for every Microsoft Team and SharePoint site. Each site must have a designated owner responsible for managing members and periodically reviewing access rights. This simple step drastically reduces the risk of accidental data leaks or unauthorized access. Our guide to SharePoint strategy and governance provides a deeper look at building these foundational controls.
Effective governance in Microsoft 365 means shifting from a default "open" model to a "least privilege" model. Team members should only have access to the specific data and tools required to perform their jobs—nothing more.
Ensuring Compliance and Business Continuity
Governance within Microsoft 365 is also your primary tool for meeting regulatory requirements, such as data residency laws that dictate where specific types of information must be stored. You can configure your environment to ensure that certain SharePoint sites or user data remain within a designated geographic region, like Canada, to satisfy legal obligations.
Furthermore, a well-governed environment is more resilient. By standardizing configurations and access controls, you simplify your entire digital workspace. This makes it easier to back up critical data, restore services after an incident, and maintain business continuity with minimal disruption. It is practical risk management applied directly where your team works.
Your Roadmap for Implementing IT Governance
Knowing where to begin with IT governance is often the greatest challenge. The concept can seem large and abstract, but a structured approach makes it a manageable process. This roadmap offers a practical, step-by-step plan for business leaders ready to establish a governance program that aligns with their organization's goals.
A successful program is always designed from the top down, starting with clear business objectives defined by leadership. From there, it becomes a continuous cycle of assessment, policy development, implementation, and improvement.
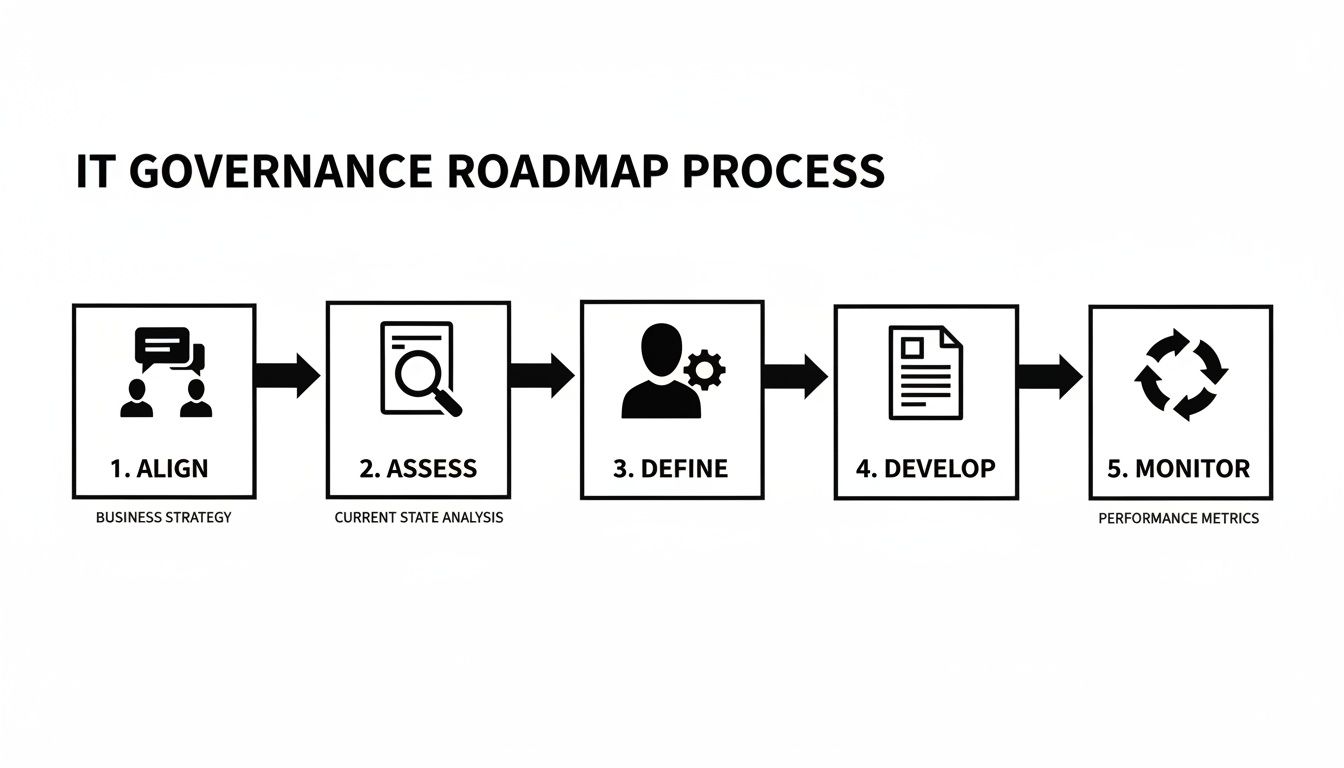
This visual demonstrates that implementation is a structured, repeatable process, not a one-time project. This ensures your governance framework adapts as your business evolves.
Step 1: Align Leadership and Define Outcomes
The first step is to convene key stakeholders to agree on the why. Is the primary goal to reduce cybersecurity risk, prepare for a regulatory audit, control escalating technology costs, or improve operational reliability? Defining these business outcomes is critical, as they become the metrics against which the program's success will be measured. Without this initial alignment, conflicting priorities can undermine the entire effort.
Step 2: Assess Current Risks and Capabilities
With clear goals established, you need an accurate picture of your starting point. This requires a thorough assessment of your current IT environment. What are your most significant security vulnerabilities? Where are the compliance gaps? Do you have undocumented systems ("shadow IT") exposing the business to unknown threats? This honest and comprehensive assessment—covering data security, access controls, vendor management, and disaster recovery—will identify your most urgent priorities.
A proper risk assessment is not about assigning blame; it is about establishing a factual baseline. It provides the data needed to make informed, strategic decisions about where to invest time and resources for the greatest impact on business resilience.
Step 3: Define Roles and Responsibilities
Governance without clear ownership is destined to fail. This stage is about assigning accountability. Who is responsible for overseeing cybersecurity risk? Who has the authority to approve new technology investments? Who is tasked with ensuring compliance with data protection laws? For many growing businesses, engaging a Virtual CIO (vCIO) provides the senior-level strategic oversight needed to guide this process and bridge the gap between business leadership and technical execution.
Step 4: Develop and Document Foundational Policies
Using the insights from your risk assessment, you can begin drafting your core IT policies. These documents serve as the practical rulebook that guides daily operations. Start with the most critical policies:
- Acceptable Use Policy: Defines how employees are permitted to use company technology resources.
- Information Security Policy: Outlines the technical and administrative controls for protecting company and client data.
- Access Control Policy: Specifies who can access which systems and data, and under what conditions.
- Incident Response Plan: Details the exact steps to be taken in the event of a security breach.
Step 5: Monitor, Measure, and Improve Continuously
IT governance is not a "set it and forget it" project; it is an ongoing cycle of improvement. This final step involves regularly reviewing policies, monitoring for new threats, and measuring performance against the business outcomes defined in step one. This continuous loop ensures your governance framework remains relevant and effective as technology, regulations, and your business goals change over time.
The Role of a Virtual CIO in Your Governance Strategy
Effective IT governance requires more than just a set of policies; it demands executive-level leadership. For many growing organizations, hiring a full-time Chief Information Officer (CIO) is not financially feasible. This is precisely where a Virtual CIO (vCIO) provides value, offering the senior expertise needed to direct your governance strategy on a fractional basis.
A vCIO acts as the bridge between your high-level business goals and your day-to-day technology operations. They translate broad objectives—like improving security posture or controlling costs—into a practical, actionable IT roadmap. This strategic guidance ensures your governance framework is a living part of your business operations, not just a document on a shelf.
Strategic Leadership and Risk Management
A vCIO’s primary role within a governance framework is to provide strategic direction. They take ownership of the IT strategy, ensuring that every technology decision aligns with the company's long-term objectives. This involves a continuous cycle of strategic planning, technology budgeting, and performance monitoring.
Working directly with your leadership team, a vCIO helps define the organization's risk tolerance. Based on that, they implement the appropriate controls and policies to manage those risks, whether they stem from cybersecurity threats, operational vulnerabilities, or regulatory compliance gaps. This proactive, business-focused approach to risk management is the foundation of a resilient and secure organization.
A Virtual CIO brings board-level technology expertise to your organization on a fractional basis. They provide the strategic oversight needed to make informed decisions, manage risk, and ensure your technology investments deliver measurable returns.
Driving Compliance and Informed Decision-Making
Navigating the complex maze of regulatory compliance is a significant challenge for any business. A vCIO stays current with evolving regulations and ensures your IT environment meets all necessary requirements. They also oversee the documentation and reporting required for audits, providing leadership with the confidence that the business is protected from costly non-compliance penalties.
This oversight is especially critical in regions where digital governance frameworks are developing. Recent data from the 2023 OECD–IDB Digital Government Index shows that countries in Latin America and the Caribbean have achieved only 22% progress in key implementation areas, compared to 53% among OECD members. This gap often requires private companies to set their own high standards for governance. Learn more about these regional AI governance findings.
Finally, a vCIO provides clear, jargon-free reports to leadership. By translating complex technical metrics into plain business language, they empower the executive team to make better-informed decisions. This ensures that everyone understands the value and risks associated with technology, turning complex IT issues into manageable business conversations. To see how this works in practice, explore the benefits of fractional CIO services for your business growth.
Common Questions About IT Governance
As business leaders explore IT governance, several key questions frequently arise. Clear answers can demystify the topic and provide the confidence needed to move forward. Here, we address the most common queries with practical, business-focused insights.
Is IT Governance Only for Large Corporations?
No. While the term may sound like it belongs in a large enterprise, the core principles of IT governance are essential for businesses of any size, especially those handling sensitive client data or operating in regulated industries. For a small or midsize business (SMB), governance is simply a structured approach to managing cybersecurity risks, maximizing technology investments, and building a secure foundation for growth. A practical implementation, often guided by an expert partner, delivers the necessary strategic oversight without the bureaucracy of a large corporation.
What Is the Difference Between IT Governance and IT Management?
This is a critical distinction. In short, IT governance sets the strategic direction, while IT management executes the plan.
- Governance is about the what and the why. It involves the leadership team defining high-level goals, determining the organization's risk appetite, and approving key policies.
- Management is about the how. It involves the IT team or a managed services provider implementing those policies, running daily operations, maintaining systems, and working to achieve the targets set by the governance framework.
Governance provides the rulebook, and management executes the plays.
How Long Does It Take to Implement an IT Governance Framework?
Implementation is a continuous journey, not a one-time project. With expert guidance, you can establish the foundational elements—such as identifying major risks, defining roles, and documenting critical security policies—within a few months. These initial steps deliver immediate value by addressing your most significant vulnerabilities first.
However, mature IT governance is a cycle of continuous improvement. The ultimate goal is to build a program that evolves with your business, technology, and the changing regulatory landscape. It should become an integrated part of your operational rhythm, not a standalone project with an end date.
A well-defined IT governance strategy is the cornerstone of a secure, efficient, and resilient business. To build a framework that aligns with your specific goals, it helps to have an experienced partner at your side. The team at Tricord I.T Solutions provides the strategic guidance and hands-on support needed to translate governance principles into practical, value-driven results. Schedule a consultation to discuss your IT governance roadmap.