Network support services are the full range of professional IT functions that keep a business's digital infrastructure running reliably, securely, and efficiently. This includes proactive monitoring to prevent downtime, strategic planning for future growth, and comprehensive security management to protect sensitive company and client data. The primary goal is to ensure business operations continue without interruption.
For business owners and executives, effective network support is not just a technical function—it is a critical component of risk management, cost control, and operational stability. A well-managed network allows your team to access critical applications, collaborate effectively, and serve clients without the disruption caused by technology failures.
Why Network Support is a Foundational Business Investment

Your business network is the central nervous system of your entire organization. It manages the flow of data, powers communication, and protects your assets from external threats. When the network is stable and secure, operations are seamless. When it fails, work can grind to a halt, impacting revenue, client trust, and staff productivity.
Effective network support services move beyond the traditional "break-fix" model, which only addresses problems after they occur. Modern support is a proactive discipline focused on building a resilient and cost-effective technology environment. The objective is to minimize operational risk and ensure your digital backbone consistently supports your business goals.
Aligning Technology with Business Objectives
A mature approach to network support is about strategic alignment, not just technical maintenance. A qualified provider works to understand your operational needs and long-term goals, ensuring the network is not just stable today but also prepared for future demands. This alignment delivers tangible business value:
- Improved Efficiency: Optimizing network performance to accelerate access to essential cloud services like Microsoft 365 and SharePoint.
- Cost Control: Transitioning to a predictable service model that eliminates surprise expenses from unexpected downtime or security incidents.
- Risk Mitigation: Proactively identifying and resolving security vulnerabilities before they can be exploited by attackers.
- Scalable Growth: Designing an infrastructure that can easily accommodate more users, new locations, or increased data volume without costly overhauls.
The demand for robust network services is increasing as businesses adapt to remote and hybrid work models. For example, the market for service provider network infrastructure in the Caribbean is projected to reach US$483.61 million by 2025. This growth, detailed in network infrastructure trends on Statista.com, underscores the critical need for reliable connectivity.
Ultimately, investing in professional network support is a strategic business decision that directly impacts productivity, security, and financial performance. It transforms your network from a potential liability into a powerful asset that enables sustainable growth. To understand how this fits into a broader IT strategy, explore the benefits of comprehensive managed IT services.
Key Components of Network Support Services
Effective network support is not a single service but a framework of interconnected functions designed to create a reliable and secure IT environment. These components work together to prevent problems, protect data, and ensure your technology serves as a business asset, not a liability.
At its core, network support ensures the seamless flow of information across your organization. This includes everything from the physical hardware in your office to the cloud services your team uses daily. Each component has a specific function, and their coordinated operation delivers the reliability, security, and performance your business requires.
Proactive Monitoring and Incident Response
The foundation of modern support is proactive monitoring. Instead of waiting for an employee to report a slow connection or system outage, a support partner continuously watches network performance. This 24/7 network monitoring allows technicians to identify potential issues—such as unusual traffic patterns or failing hardware—long before they impact your operations.
When an issue does arise, a structured incident response plan is activated. This is a methodical process to identify the root cause, resolve the problem, and restore services as quickly as possible, minimizing business disruption.
A well-defined incident response plan can significantly reduce the financial and operational impact of a technology failure or security breach. It transforms a potential crisis into a manageable event through a swift, coordinated, and effective resolution.
Security and Patch Management
In today's threat landscape, security cannot be an afterthought; it must be integrated into every aspect of network support. This involves actively managing firewalls, configuring secure access controls, and deploying systems to detect and block intrusions.
A critical component of this is patch management. Software vulnerabilities are a primary entry point for cyber attackers. A dedicated support team ensures that all network devices—routers, switches, firewalls—and servers receive security updates as soon as they are available. This essential task closes security gaps before they can be exploited, protecting your company's sensitive data.
Network Design and Connectivity Solutions
Effective network support also involves strategic planning. As your business grows, your network must scale without causing performance bottlenecks or requiring a complete overhaul. A skilled provider helps design a network that is both efficient today and built to handle future demands. This proactive approach to managed infrastructure is key to long-term stability.
This strategic oversight extends to all aspects of business connectivity:
- LAN/WAN Management: Optimizing your Local Area Network (office) and Wide Area Network (connecting multiple sites and the internet) for speed and reliability.
- Secure Remote Access (VPN): Implementing and managing Virtual Private Networks (VPNs) so remote employees can securely access company resources.
- Wi-Fi Optimization: Designing a robust and secure wireless network that provides seamless coverage without introducing security risks.
- VoIP Support: Managing your Voice over IP phone system to ensure clear, dependable communication for your team and clients.
By integrating these components, network support services provide a complete solution that protects your business, improves productivity, and builds a stable foundation for growth.
Proactive vs. Reactive Support: A Critical Business Decision
When managing your business network, you have two fundamental choices: a proactive model, typically through a managed services provider for a fixed monthly fee, or a reactive model, where you call for help only when something breaks.
This decision directly impacts your operational risk, budget predictability, and business continuity. One approach focuses on preventing problems, while the other focuses on resolving them after they have already caused disruption. Your choice defines your organization's resilience against downtime and security threats.
The Reactive "Break-Fix" Model
The break-fix model is straightforward: when your network fails, you call a technician, who then bills you for their time and any required parts. On the surface, this may seem cost-effective because you only pay for services when a problem occurs.
However, the hidden costs can be substantial. An unexpected bill for a major server failure or security breach can disrupt your budget. More importantly, the incentives are misaligned. A break-fix provider generates revenue only when your systems are down. Their financial success is tied to your problems, creating a direct conflict with your goal of maintaining uptime.
This model often results in:
- Extended Downtime: Problems are only discovered after they have already impacted operations, leading to longer resolution times.
- Unpredictable Costs: Budgeting becomes difficult, as a single incident can lead to thousands of dollars in emergency fees.
- Lack of Strategic Guidance: The technician's role is to fix the immediate issue, not to help you plan for growth or optimize your technology.
The Proactive Managed Services Model
A proactive model operates on a different principle. You pay a predictable, fixed monthly fee to a partner who manages and monitors your network 24/7. This structure aligns incentives. Your provider's profitability now depends on keeping your network running flawlessly. Downtime costs them time and resources, so they are highly motivated to prevent issues before they occur.
This partnership is the basis of modern managed IT services. The focus shifts from reaction to prevention. Your IT provider's goals align with yours: maximize uptime, strengthen security, and improve efficiency.
Under a proactive support model, the IT provider acts as a strategic partner. Their success is directly tied to your operational stability, creating a powerful incentive to maintain a healthy, resilient, and secure network.
This approach facilitates strategic planning, regular maintenance, and continuous security monitoring. Minor issues are identified and resolved before they can escalate into business-disrupting outages, saving you from the stress and high costs of emergency repairs.
To illustrate the differences, the following table compares the two models.
Comparing Network Support Models: Fixed Fee vs. Break-Fix
This side-by-side comparison helps businesses evaluate the financial and operational implications of each IT support model.
| Criteria | Fixed Monthly Fee (Managed Services) | Break-Fix (Hourly Support) |
|---|---|---|
| Cost Structure | Predictable, fixed monthly fee for all-inclusive support. | Unpredictable hourly rates plus the cost of parts. |
| Business Alignment | The provider is incentivized to maximize your uptime and prevent issues. | The provider profits from your downtime and technical problems. |
| Response Time | Guaranteed response times defined in a Service Level Agreement (SLA). | Response is based on technician availability, often with no guarantee. |
| Strategic Value | Includes long-term planning, security guidance, and technology roadmaps. | Focused solely on resolving the immediate problem at hand. |
| Downtime Risk | Minimized through 24/7 monitoring and proactive maintenance. | High, as problems are only addressed after they have occurred. |
Ultimately, the choice depends on whether you view IT as a reactive expense or a strategic investment. While the break-fix model may appear cheaper initially, the proactive approach delivers the stability and foresight necessary for a business to thrive.
The Critical Role of Security and Compliance in Network Support
Modern network support is inseparable from cybersecurity and regulatory compliance. Your network is no longer just a productivity tool; it is the first line of defense protecting your most valuable business and client data. A poorly managed network creates significant exposure to financial loss, reputational damage, and legal liability.
For this reason, contemporary network support is built on a foundation of security. It requires a strategic approach that integrates security into every layer of your infrastructure, transforming your network from a potential vulnerability into a powerful tool for risk management.
Navigating Industry-Specific Regulations
For businesses in regulated industries such as law, healthcare, or finance, compliance is a core operational requirement. Your network configuration is directly tied to your ability to meet standards like PIPEDA, HIPAA, and other data privacy regulations.
A knowledgeable network support partner understands these requirements and knows how to configure your network to meet them. Key actions include:
- Access Controls: Implementing strict policies to ensure only authorized individuals can access sensitive information, a fundamental requirement of most compliance frameworks.
- Secure Data Transmission: Using encryption and secure protocols like VPNs to protect data both within your office and when accessed remotely.
- Continuous Monitoring: Actively monitoring network traffic for signs of unauthorized access or anomalous activity that could indicate a breach.
These are not just compliance checklist items; they are practical, real-world measures that protect your business from liability, build client trust, and ensure operational continuity.
Practical Risk Mitigation and Audit Readiness
A secure network is a defensible one. This is achieved through a layered security strategy where multiple tools and processes work together to protect your data. Many businesses rely on managed network security solutions to provide this comprehensive protection and maintain compliance.
The core of this strategy includes firewalls to control access, intrusion detection systems to identify threats, and proactive patch management to close security vulnerabilities. This constant vigilance ensures you are always prepared for a potential audit.
An IT partner with deep compliance expertise helps you build a clear, documented record of your security measures. This documentation is invaluable during an audit, proving due diligence and a proactive approach to data protection.
The need for this integrated approach is growing. The Caribbean mobile data market is expected to generate $4.8 billion in revenue by 2025, driven by businesses requiring high-speed, secure connections. This growth highlights the urgent need for robust network support that can defend against the evolving threats in an increasingly digital world.
Ultimately, a strong security posture is the result of deliberate planning and consistent management. By partnering with a provider skilled in both network support and cybersecurity, you build a resilient foundation that protects your assets and reputation. To learn more, our guide on advanced cybersecurity frameworks provides further details on safeguarding sensitive data.
How to Choose the Right Network Support Partner
Selecting an IT partner is a critical business decision. The goal is not just to find a vendor to fix technical issues but to secure a strategic advisor who will protect your operations, manage risk, and support your growth. You must look beyond sales pitches to find a team with the right expertise and business acumen.
A thorough evaluation process helps you identify a provider who understands your business objectives and offers more than just reactive fixes. The aim is to find a partner who aligns with your company culture, provides strategic value, and has the experience to serve as a trusted advisor.
Key Evaluation Criteria
Before interviewing potential partners, establish clear evaluation criteria to compare providers effectively. Focus on these core areas to create a solid shortlist.
Your evaluation should include:
- Technical Expertise and Certifications: Does the team hold relevant certifications from major vendors like Microsoft or Cisco? Can they demonstrate deep knowledge in critical areas like cybersecurity, cloud infrastructure, and network design?
- Industry-Specific Experience: Have they worked with businesses in your sector, such as law, healthcare, or finance? Understanding the compliance and operational challenges specific to your industry is essential.
- Service Level Agreements (SLAs): A reputable partner formalizes their commitments in writing. The SLA should clearly define guaranteed response times, resolution targets, and uptime commitments.
- Proactive vs. Reactive Approach: Is their service model built around preventing problems, or do they primarily respond to issues after they occur? A true partner works continuously in the background to maintain stability.
- Scalability and Future-Proofing: Can they support your business as it grows? They should be able to discuss how they help clients develop a technology roadmap that addresses future needs, not just current problems.
Insightful Questions to Ask Potential Providers
Once you have a shortlist, the vetting process begins. The questions you ask should go beyond technical specifications to uncover their service philosophy, operational processes, and approach to client relationships.
Choosing an IT partner is like hiring a key executive. Their ability to communicate clearly, solve problems methodically, and align with your business vision is just as important as their technical skill set.
Use these questions to guide your conversations and assess their true capabilities:
-
"How do you proactively identify potential network issues before they impact our operations?"
- This question assesses their commitment to preventative maintenance. A strong partner will describe their monitoring tools, regular health checks, and processes for early detection.
-
"Can you walk me through your incident response process, from detection to resolution?"
- Listen for a structured, methodical approach. They should outline clear steps for communication, escalation, root cause analysis, and post-incident review to prevent recurrence.
-
"How do you stay current with emerging cybersecurity threats and new compliance requirements?"
- A confident provider will discuss ongoing team training, industry certifications, and how they integrate new security protocols into their clients' environments.
-
"Can you provide anonymized examples of how you have helped a business similar to ours achieve its objectives?"
- This question tests their industry experience and ability to connect technology solutions to tangible business outcomes, such as improved efficiency or reduced risk.
By focusing on these practical criteria and asking insightful questions, you can look past generic claims and find a network support partner who can genuinely protect and advance your business.
Building a Strategic Technology Roadmap
Effective network support is not just about resolving today's issues; it is about preparing for tomorrow's growth. A strategic technology roadmap is a clear, actionable plan that aligns your IT investments directly with your business objectives.
Without a roadmap, technology decisions are often reactive, driven by immediate problems rather than long-term opportunities. A well-designed plan transforms your network from a necessary cost into a strategic asset. It provides a structured path for modernizing systems, strengthening security, and improving efficiency over time. This proactive planning helps control costs, manage risk, and ensure your technology can scale with your business.
From Assessment to Implementation: A Practical Example
Consider a mid-sized law firm struggling with unreliable remote access and an inefficient document management system. Their network was slow, and their aging on-premise servers posed significant operational and security risks. They required a sustainable, long-term strategy, not a quick fix.
The process began with a comprehensive risk assessment conducted with a technology partner. This initial step was crucial for identifying critical vulnerabilities and performance bottlenecks. The assessment findings became the blueprint for a multi-phase roadmap designed to align their technology with their business goals.
The roadmap included several key initiatives:
- Phase 1: Network Modernization: The first priority was upgrading the core network hardware to improve speed and reliability. This phase also included implementing a secure VPN solution to support remote work effectively.
- Phase 2: Cloud Migration: The firm then executed a planned migration to Microsoft 365 and SharePoint. This moved their operations to a more secure, scalable, and collaborative cloud environment.
- Phase 3: Ongoing Strategic Guidance: Finally, they engaged a Fractional CIO to provide continuous oversight, ensuring the technology plan remained aligned with the firm’s evolving business strategy and compliance requirements.
This diagram illustrates the high-level process for starting such a journey by selecting the right partner.
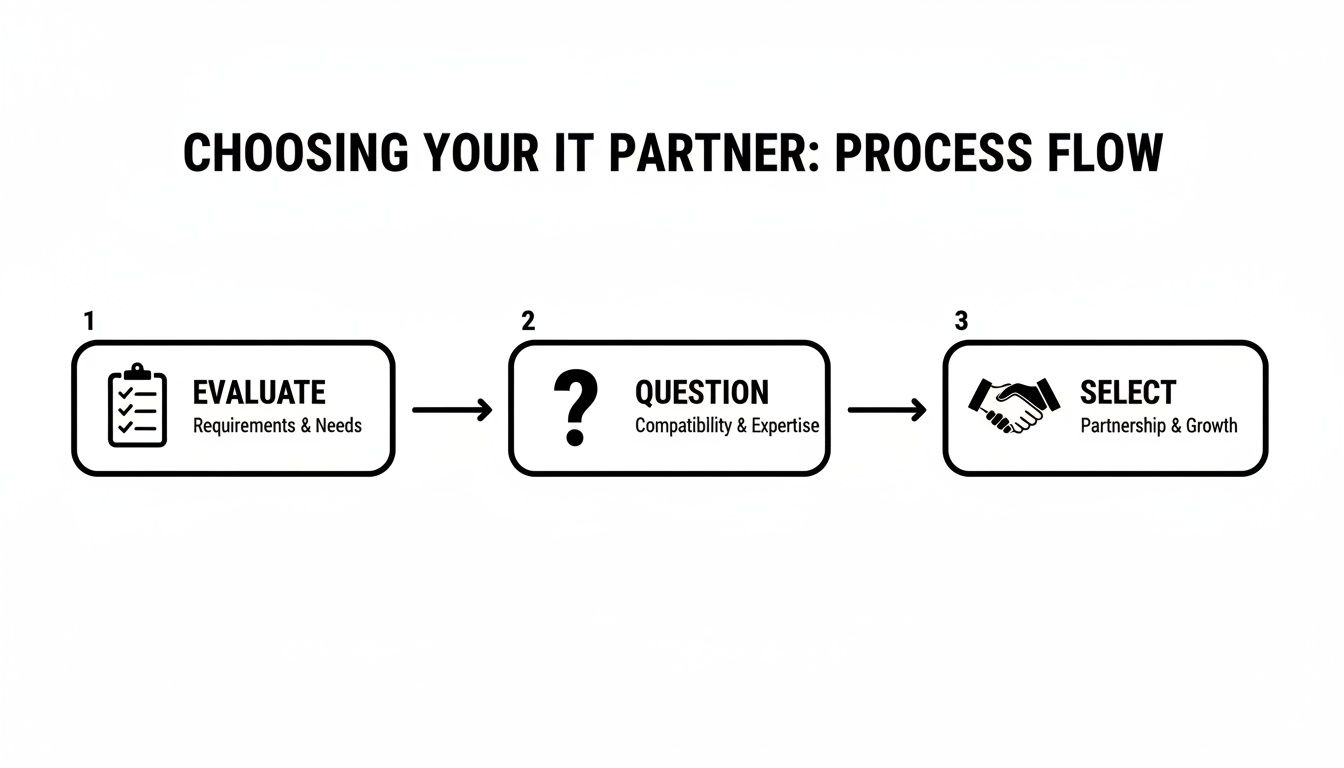
This structured approach—evaluating needs, asking the right questions, and selecting a strategic partner—is the first step in transforming technology from a challenge into a driver of growth.
The Return on Strategic Investment
For the law firm, the results were transformative. The migration to Microsoft 365 streamlined document management and collaboration, directly improving team efficiency. The modern network infrastructure virtually eliminated downtime and provided all employees with secure, reliable access from any location.
A strategic roadmap transforms technology spending from a reactive expense into a predictable investment. It allows businesses to budget effectively, mitigate risks proactively, and ensure every dollar spent on IT drives a measurable business outcome.
The ongoing guidance from the Fractional CIO was the most critical component, ensuring that technology decisions always supported the firm's business objectives. This strategic oversight is what distinguishes basic IT support from a true technology partnership.
This example demonstrates a key principle: your network is the backbone of your business. Investing in a strategic roadmap is an investment in your company’s future resilience, security, and growth.
What to Do Next
Developing a technology roadmap begins with a clear assessment of your current situation. A thorough review of your existing infrastructure, security posture, and business processes is the essential first step to creating a plan that delivers tangible value.
If you are ready to align your technology with your business goals, consider scheduling a consultation. An expert review can help identify opportunities to improve efficiency, reduce risk, and build a scalable foundation for the future.
Frequently Asked Questions About Network Support
Business leaders often have practical questions about network support services. Understanding the costs, scope, and service guarantees is essential for making an informed decision. Here are answers to some of the most common questions.
How Much Do Network Support Services Cost?
For most small and mid-sized businesses, a fixed-fee managed services plan typically costs between $100 and $250 per user per month. This price generally includes proactive monitoring, security management, helpdesk support, and strategic IT guidance.
The final cost can vary based on the number of users, the complexity of your network, and any specific compliance requirements, such as those in healthcare or finance. The purpose of a fixed-fee model is to provide a predictable monthly cost and align the provider's incentives with your goal of maintaining a flawless network.
What is the Difference Between General IT and Network Support?
While closely related, these two types of support address different aspects of your technology environment.
- General IT Support focuses on the end-user and their tools. This includes managing laptops, desktops, software applications like Microsoft Office, and resolving individual employee issues through a helpdesk.
- Network Support focuses on the underlying infrastructure that enables all work to happen. This involves managing routers, switches, firewalls, and Wi-Fi to ensure data flows reliably and securely between all systems, whether they are on-premise or in the cloud.
A comprehensive IT partner provides both, ensuring your entire technology ecosystem functions seamlessly.
What Should I Expect from a Service Level Agreement (SLA)?
A Service Level Agreement (SLA) is a formal contract that defines the standards of service you will receive. It translates verbal promises into measurable, enforceable commitments and sets clear expectations.
A strong SLA is your assurance of quality and accountability. It should explicitly detail guaranteed response times for critical issues, uptime percentages for key systems, and the process for escalating urgent problems to ensure swift resolution.
Without a clear SLA, you are left uncertain about how or when a critical issue will be addressed—a risk no business should accept. It is a non-negotiable component of any professional IT partnership.
At Tricord I.T Solutions, we build strategic technology roadmaps that align with your business goals, providing the security, reliability, and expert guidance you need to thrive. Learn more at https://bvc.ee2.myftpupload.com.

