Cloud managed IT services represent a fundamental shift in how businesses manage technology. Instead of maintaining complex systems in-house, companies partner with expert providers who handle the monitoring, security, and maintenance of their cloud infrastructure. This model ensures technology is reliable, secure, and aligned with core business objectives, allowing leadership teams to focus on growth instead of technical issues.
This approach is about outsourcing the day-to-day management of your cloud environment to a specialized firm. A provider takes responsibility for your servers, applications, data, and cybersecurity, offloading the technical burden so your team can focus on its primary roles. It is a strategic partnership designed to reduce risk, control costs, and improve operational stability.
What Are Cloud Managed IT Services?
Think of a cloud managed IT services provider as a professional management firm for your digital infrastructure. Instead of your team worrying about server maintenance, security patches, or system failures, a dedicated partner handles everything proactively. Their goal is to ensure your technology environment is secure, efficient, and fully operational, supporting your business rather than disrupting it.
This partnership involves an expert firm taking full accountability for your cloud environment, including servers, networks, applications, and cybersecurity. The primary benefit is offloading the complex and time-consuming tasks of IT management, which frees your internal resources to concentrate on strategic initiatives. When evaluating partners, it's helpful to understand the scope of modern managed cloud services and how they deliver tangible business outcomes.
The Core Components and Their Business Impact
While specific offerings vary, most cloud managed IT services include several key components, each delivering a direct operational benefit. A strong partnership ensures technology functions as a business enabler, not a source of risk or unpredictable costs. To understand the broader context, you can explore the foundational principles of managed IT services and their application across different business models.
The table below summarizes the core components and their direct impact on your business.
Cloud Managed IT Services At a Glance
| Core Service Component | Business Impact |
|---|---|
| Proactive Infrastructure Management | Ensures system reliability and minimizes costly downtime by continuously monitoring and optimizing servers, storage, and networks. |
| Comprehensive Cybersecurity | Protects sensitive data and intellectual property from threats, helping maintain compliance and avoid reputational damage from breaches. |
| Strategic Technology Guidance | Aligns technology investments with long-term business goals, ensuring a clear roadmap for growth and efficiency. |
| Application & User Support | Empowers your team with reliable access to critical tools like Microsoft 365, improving productivity and collaboration. |
| Predictable Cost Model | Converts unpredictable capital expenditures into a fixed monthly operational cost, simplifying budgeting and improving financial control. |
Each of these components works in concert to create a technology environment that is not just stable but also a strategic asset that supports growth and protects your bottom line.
Understanding the Core Components of a Modern Cloud Strategy
A comprehensive cloud strategy is more than reactive IT support; it is a multi-layered approach that aligns technology with business objectives. Understanding its components helps you evaluate whether a potential partner offers a complete service or just a basic help desk. A true partnership is built on four pillars: infrastructure, security, strategy, and application support.
The diagram below illustrates how these functions establish the foundation for achieving key business goals like enhanced security, controlled costs, and operational reliability.
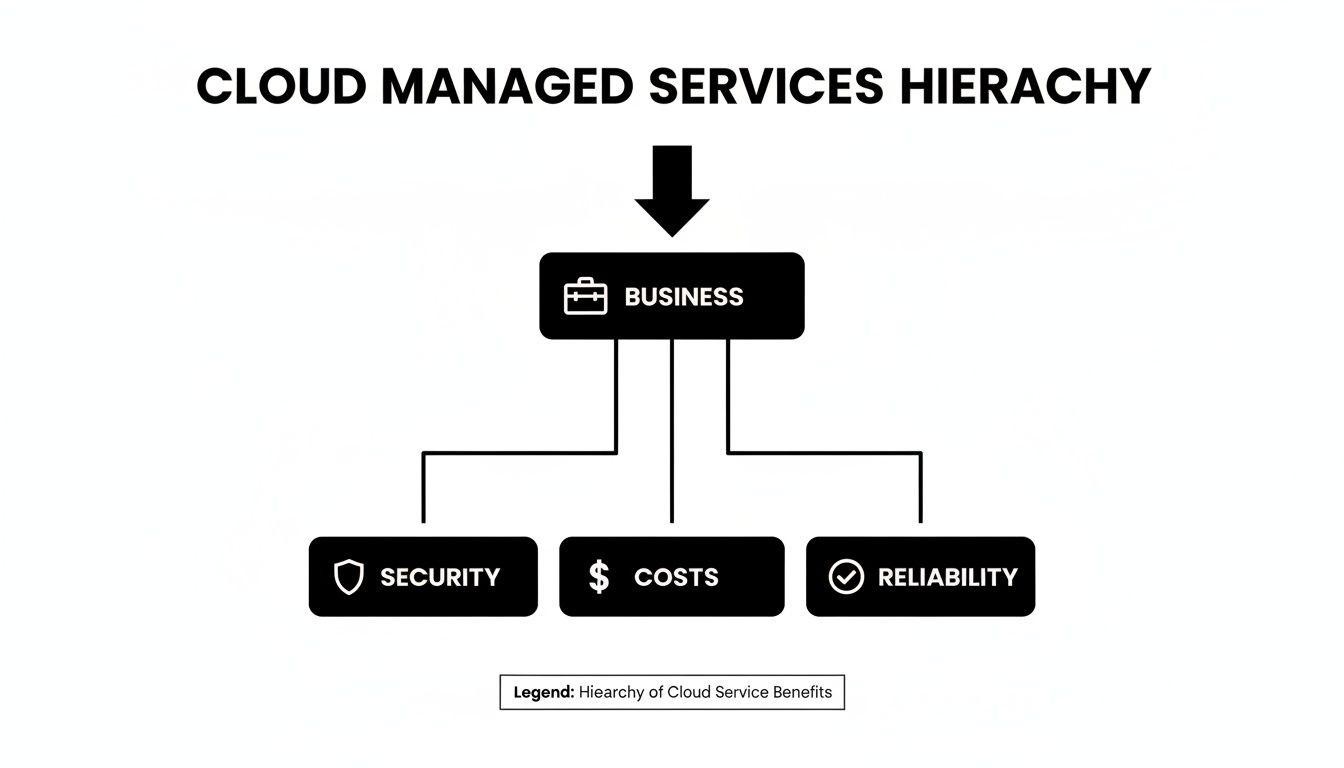
As shown, a successful business outcome depends on a foundation where security, cost management, and operational uptime are actively managed through dedicated cloud services.
Proactive Infrastructure Management
The foundation of any cloud managed service is the health and performance of your digital infrastructure. This involves preventing outages before they happen, rather than reacting to them after the fact.
Proactive management means continuous, 24/7 monitoring of servers, networks, and data storage. An expert team identifies and resolves performance bottlenecks, potential hardware failures, and unusual activity before they escalate into business-disrupting downtime. This approach ensures your systems run smoothly and reliably, maintaining team productivity.
Robust Cybersecurity Services
In today's environment, cybersecurity cannot be an afterthought. An effective cloud partner integrates security into every aspect of your IT operations to build a resilient defense against constant threats. This is a non-negotiable component of any responsible cloud managed IT services plan.
Core cybersecurity services should include:
- Advanced Threat Detection: Using sophisticated tools to identify and neutralize malware, phishing attempts, and other malicious activity in real-time.
- Incident Response Planning: A clear, pre-planned protocol for responding to a breach, minimizing damage and ensuring swift recovery.
- Compliance Management: Ensuring your IT environment meets the strict regulatory requirements of your industry, such as those in the legal, healthcare, or financial sectors.
This proactive security posture protects sensitive data, preserves your reputation, and helps avoid the significant financial and operational costs of a security incident.
Strategic Technology Guidance
Technology should be a tool that drives your business forward, not a cost center that holds it back. Strategic guidance, often provided by a Virtual Chief Information Officer (vCIO), is invaluable. A vCIO acts as a high-level technology advisor for your business.
They work with your leadership team to create a technology roadmap aligned with your long-term goals. This includes making informed decisions about new software, planning for infrastructure upgrades, and ensuring your IT budget generates a clear return on investment.
Specialized Application Support
Your business relies on specific applications, with platforms like Microsoft 365 and SharePoint often central to collaboration and data management. Specialized support for these critical tools is a key part of a modern cloud strategy.
This extends beyond basic user help to include optimizing configurations for security and efficiency, managing user permissions to protect sensitive information, and ensuring seamless integration with other business systems. Expert support for these applications empowers your team to collaborate securely and efficiently. Some firms also integrate advanced tools like AI-powered support solutions like supportGPT to resolve user issues more quickly.
Market trends underscore the rapid adoption of these services. The growth of the managed services market in Canada is largely driven by sectors like finance and legal that demand secure, scalable, and compliant solutions. For business leaders, this signals that managed cloud services are no longer just an option—they are a strategic necessity for remaining competitive.
What This Means for Your Business
Technical features are only valuable if they benefit your business. For owners and executives, the key question is how cloud managed IT services deliver real-world advantages like reduced risk, predictable costs, and operational stability. The answer lies in shifting from a reactive, break-fix approach to proactively managing technology as a strategic asset.
This is where a partnership with a cloud managed services provider delivers its greatest value. It connects every technical action—from security monitoring to system updates—to a tangible business outcome that strengthens your financial position and competitive advantage.

Strengthen Your Security and Compliance Posture
One of the most critical benefits is a significant improvement in your company’s security and compliance standing. In regulated fields such as law, finance, and healthcare, a single data breach or compliance failure can result in substantial fines, reputational damage, and loss of client trust.
A managed services provider acts as your dedicated security guardian, building and managing a layered defense system designed to counter threats while ensuring your infrastructure meets strict industry regulations.
This proactive security management includes:
- Continuous Threat Monitoring: Your networks are monitored 24/7 for suspicious activity, allowing threats to be identified and neutralized before they cause harm.
- Regular Security Patching: All systems and software are consistently updated to close vulnerabilities that cybercriminals exploit.
- Compliance Alignment: Your cloud environment is configured to meet specific regulatory standards, providing the documentation and audit trails needed for verification.
This constant vigilance protects your business from costly breaches and simplifies the challenge of maintaining regulatory compliance.
Achieve Predictable Costs and Financial Control
Unexpected IT expenses can disrupt budgets. Emergency hardware replacements, unforeseen software license fees, and hourly break-fix support bills create financial uncertainty. Cloud managed services replace this unpredictable model with a straightforward, fixed monthly fee.
The shift from a Capital Expenditure (CapEx) to an Operational Expenditure (OpEx) model is a game-changer for financial planning. It eliminates surprise IT bills, allowing for more accurate budgeting and freeing up capital for core business growth.
This financial predictability makes it easier to forecast expenses and invest confidently in other areas of your business, knowing your technology costs are stable. It is a primary driver behind the projected growth of the Canadian managed services market, which is expected to reach US$52.1 billion by 2033. This trend is fueled by businesses in regulated sectors seeking both robust security and cost optimization.
Gain Access to Specialized Expertise
Hiring, training, and retaining a full-time, in-house team of IT specialists with deep expertise in cybersecurity, cloud architecture, and specific platforms is extremely expensive. For most small to mid-sized businesses, it is not practical.
Partnering with a managed services provider gives you immediate access to an entire team of seasoned professionals for a fraction of the cost. You gain a deep bench of specialized knowledge without the overhead of salaries, benefits, and ongoing training. Whether you need an expert to secure your cloud environment or optimize your Microsoft 365 setup, the right skills are available when you need them.
Enhance Operational Resilience and Focus
Ultimately, business leaders want their technology to work reliably. The greatest benefit of cloud managed IT services is improved operational resilience. By minimizing downtime and resolving issues quickly, a provider ensures your team remains productive and focused on their core responsibilities.
Instead of being sidetracked by IT problems, your staff can concentrate on serving clients, developing products, and driving revenue. Offloading IT management allows your entire organization to operate more efficiently, transforming technology from a potential liability into a reliable engine for growth. To learn more, explore our detailed guide on the key benefits of managed IT services.
How to Choose the Right Cloud Managed IT Provider
Selecting a partner for your cloud managed IT services is a critical technology decision. The right provider becomes an extension of your team, while the wrong one can introduce risk, inefficiency, and frustration.
A successful choice requires a thorough evaluation of service commitments, security practices, and real-world expertise. A low-cost provider that fails during a crisis is not a bargain but a liability. You need a forward-thinking advisor, not just a reactive help desk that only fixes problems after they occur.

Scrutinize the Service Level Agreement
The Service Level Agreement (SLA) is the contract that defines the partnership. It is the most important document to review, as it sets clear, measurable expectations. Do not settle for vague promises of "fast support."
A robust SLA will specify:
- Guaranteed Response Times: How quickly they will acknowledge a support request, broken down by severity. A system-wide outage requires a much faster response than a minor user issue.
- Guaranteed Resolution Times: How long it will take them to fix the problem. A fast response is meaningless if the issue persists for days.
- Uptime Guarantees: Look for commitments of 99.9% uptime or higher for critical systems. The SLA should also outline penalties for failing to meet this standard.
- Reporting and Transparency: Details on how they will report on system performance, security incidents, and support tickets to keep you informed.
An SLA without clear metrics and penalties is a major red flag, suggesting the provider lacks confidence in their ability to deliver consistent, high-quality service.
Assess Their Cybersecurity and Incident Response Capabilities
Your provider is your first line of defense against cyber threats. It is essential to understand their security posture and how they would handle a security incident. A breach can have catastrophic consequences, so this is not an area for compromise.
Ask direct questions about their security stack, including advanced threat detection, proactive vulnerability management, and employee security training. Crucially, ask to see their Incident Response Plan. A well-documented plan demonstrates a structured process for containing a threat, eradicating it, and recovering your systems with minimal disruption.
A provider's true value is often revealed during a crisis. A detailed and rehearsed incident response plan is a clear indicator of a mature and reliable security partner who is prepared to protect your business when it matters most.
Verify Their Expertise in Your Core Platforms
Many businesses rely on platforms like Microsoft 365 and SharePoint for daily operations. Generic IT support is insufficient; you need a provider with deep, proven expertise in the technologies that power your business.
Request case studies or references from clients in your industry using the same platforms. This specialized knowledge is critical for optimizing security, ensuring compliance, and maximizing your return on investment. A provider who understands Microsoft 365, for example, can implement proper data governance and security controls that a generalist might overlook. This focus is increasingly important as businesses navigate the cloud ROI challenges facing Canadian CIOs and seek partners who can deliver tangible value.
Putting It All Together: An Evaluation Checklist
Choosing a provider can feel overwhelming, but a structured approach simplifies the process. This checklist will help you compare potential partners on the criteria that matter, ensuring you find one who aligns with your business goals.
Provider Evaluation Checklist
| Evaluation Criterion | What to Look For | Why It Matters |
|---|---|---|
| Service Level Agreement (SLA) | Clear, measurable metrics for response and resolution times, uptime guarantees (99.9%+), and penalties for non-compliance. | A strong SLA provides accountability and ensures you receive the level of service your business requires. Vague terms are a red flag. |
| Cybersecurity Posture | A multi-layered security stack (e.g., EDR, vulnerability scanning) and a well-documented Incident Response Plan. | Your provider is your frontline defense. A proactive security approach and a clear plan for emergencies are non-negotiable. |
| Platform Expertise | Demonstrated experience and certifications in your core technologies (e.g., Microsoft 365, Azure, specific industry software). | Specialized knowledge ensures your systems are optimized, secure, and compliant. Generalists may miss critical configurations. |
| Client References & Case Studies | Positive feedback from businesses of a similar size and in a similar industry. Proof of successful projects. | This validates their claims and gives you insight into the actual client experience, not just the sales pitch. |
| Monitoring & Reporting | Proactive 24/7 system monitoring, regular performance reports, and transparent ticketing systems. | You need a partner who identifies issues before they become problems and keeps you informed about your IT environment's health. |
| Strategic Guidance | Evidence of providing long-term IT roadmaps, budget planning, and advice that aligns technology with business goals. | The best partners are strategic advisors who help you plan for the future, not just fix today's problems. |
By thoroughly vetting potential providers using these criteria, you are not just buying a service—you are investing in a partnership that will be fundamental to your business's stability, security, and success.
Common Mistakes to Avoid When Outsourcing IT
Adopting a managed cloud model can transform your business, but the transition has potential pitfalls. Even with a clear understanding of the benefits, mistakes during selection and implementation can undermine the initiative. Avoiding these common errors is key to building a successful partnership that delivers real value.
Migrating Without a Clear Strategy
One of the most significant mistakes is migrating to the cloud without a detailed plan. This often occurs when businesses feel pressured to adopt cloud technology without defining what success looks like. A migration without a roadmap frequently leads to budget overruns, unexpected downtime, and a final configuration that fails to meet business needs.
A sound strategy must answer several critical questions before any data is moved:
- Which applications and workloads are suitable for the cloud?
- What are the mandatory security and compliance requirements for our data?
- How will the new cloud environment integrate with existing systems?
- What is a realistic timeline and budget for the project?
A reputable provider will insist on developing this strategic plan with you, turning a potentially chaotic process into a carefully managed transition.
Choosing a Provider Based Solely on Price
Selecting a provider based only on the lowest price is a classic false economy. A low initial cost often conceals hidden expenses, such as poor support, weak security, and vague Service Level Agreements (SLAs). These deficiencies can lead to costly downtime or a security breach that far exceeds any upfront savings.
Instead of focusing on the monthly fee, evaluate the total value. A slightly higher investment in a provider with a proven security record, robust SLAs, and deep industry knowledge provides a greater return. You are not just purchasing a service; you are investing in operational reliability and peace of mind.
Overlooking Security and Compliance from Day One
Another common error is treating security and compliance as an afterthought. For businesses in regulated industries like law, finance, or healthcare, neglecting these from the outset can lead to severe fines and reputational damage. Security must be integrated into the strategy from the beginning, not added on later.
Every decision, from the initial assessment to the final deployment, must be viewed through a security and compliance lens. This proactive approach ensures your data is protected from day one and your operations meet all necessary regulations, preventing a costly remediation process later.
Before signing a contract, verify that the provider has demonstrable experience with compliance in your specific industry and can present a multi-layered security strategy. For more context, our guide on advanced cybersecurity frameworks offers a deeper look into this topic.
Underestimating the Need for Ongoing Optimization
The work is not finished once you are in the cloud. A cloud environment is not a "set and forget" solution. Technology evolves, business needs change, and new security threats emerge constantly. A frequent mistake is failing to plan for the continuous optimization your cloud setup requires.
Your partnership should include regular strategic reviews to ensure your technology continues to support your goals. This involves refining security protocols, optimizing costs, and planning for future needs. A proactive partner helps you adapt and improve, ensuring your technology investment continues to deliver value long after the migration is complete.
Planning Your Next Steps Toward a Secure Cloud Strategy
Choosing a partner for your cloud managed IT services is a major business decision that directly impacts your company’s security, operational efficiency, and financial health. The objective is to find a proactive ally invested in your long-term success, not just a reactive service that fixes problems as they arise. This transforms IT from a necessary expense into a strategic asset that drives growth.
Charting Your Course
Before engaging with providers, conduct an internal assessment of your current IT situation. Identify recurring frustrations, potential security gaps, and operational bottlenecks that hinder your team. This first step is crucial for understanding where expert guidance can provide the most value.
A thorough internal review is the foundation of a successful cloud strategy. Understanding your specific needs, risks, and goals allows you to engage with potential partners from a position of strength and clarity, ensuring the conversation is focused on meaningful business outcomes.
Taking Action
Once you have a clear picture of your needs, the logical next step is to schedule a no-obligation consultation to discuss your specific requirements. This is an opportunity to see how a technology plan tailored to your business can address your unique challenges and support your growth.
A strategic conversation can help you:
- Clarify Your Goals: Define what a successful technology partnership would look like for your business.
- Identify Risks: Uncover potential security and compliance vulnerabilities in your current setup.
- Explore Opportunities: Learn how modern cloud solutions can improve productivity and provide better cost control.
Taking this proactive step allows you to begin building a technology strategy that not only protects your business today but also creates a scalable foundation for a secure and prosperous future.
Frequently Asked Questions About Cloud Managed IT
Business leaders often have specific questions before committing to a managed cloud model. Here are straightforward answers to the most common inquiries.
How is this different from our current IT support?
The primary difference is a proactive versus reactive approach. Traditional IT support is often a "break-fix" service—you call for help after something has already broken. This model almost guarantees unexpected downtime and recurring problems.
In contrast, cloud managed IT services focus on preventing issues. Your provider continuously monitors, maintains, and secures your systems to stop problems before they start. The goal is to keep your operations stable and secure, not just to respond to emergencies.
How does the pricing for managed services work?
Most providers use a predictable, flat-fee monthly subscription model. This fee covers a clearly defined scope of services, which typically includes 24/7 monitoring, security management, user support, and strategic guidance.
This model provides your business with complete cost predictability, eliminating surprise invoices.
When you shift unpredictable IT spending to a fixed operational cost, budgeting becomes much easier and far more accurate. You get rid of the financial roller coaster of hourly billing and unexpected hardware replacement costs, which lets you plan for the long term.
Can you manage our existing cloud environment?
Yes. A core function of a quality provider is to take over and improve an existing cloud setup. If your team is already using platforms like Microsoft 365, a new partner can integrate seamlessly and begin adding value immediately.
The process begins with a comprehensive audit of your current environment to identify security gaps, compliance risks, and inefficiencies. Based on these findings, the provider builds a clear roadmap to bring your environment up to best-practice standards, ensuring it is secure, optimized, and aligned with your business goals.
At Tricord I.T Solutions, we provide the strategic guidance and expert management your business needs to thrive securely in the cloud. If you are ready to move from reactive IT fixes to a proactive technology partnership, we invite you to schedule a consultation. Learn more about how we can build a secure, efficient, and scalable foundation for your business at https://bvc.ee2.myftpupload.com.