For small and midsize businesses, cybersecurity is no longer an IT problem—it is a core business function essential for stability, client trust, and financial health. A robust security plan is not an optional expense; it is a critical investment in your company’s future. This guide provides a straightforward roadmap for business leaders to manage digital risk effectively.
Why Cybersecurity Is a Core Business Function

A common mistake is assuming a small business is too insignificant to be a target. In reality, cybercriminals seek the path of least resistance, making businesses with perceived weaker defenses prime targets. The consequences of a single incident extend far beyond the initial financial cost, creating a cascade of operational, reputational, and legal issues that can threaten a company's survival.
The True Cost of a Cyber Incident
The financial and operational damage from a cyberattack is nearly always more severe than business leaders anticipate. According to recent data, small businesses can expect to pay an average of $120,000 to recover from a single attack. Even more concerning, 55% of SMBs stated that a financial loss of less than $50,000 would be enough to put them out of business permanently. The long-term impact is equally severe, with a significant percentage of small businesses failing within six months of a major cyber incident. You can explore more about these threats and how to defend against them.
Beyond the immediate recovery costs, the damage includes:
- Operational Disruption: A ransomware attack can halt operations for days or weeks, preventing you from serving clients and generating revenue.
- Reputational Damage: Losing client data erodes the trust built over years. This is especially damaging for professional services firms like law offices and healthcare providers that handle highly sensitive information.
- Regulatory Penalties: Failure to comply with data protection regulations can lead to significant fines and legal challenges, adding financial strain when the business is already vulnerable.
Moving from Reactive to Proactive
The necessary mindset shift is from reactive problem-solving to proactive risk management. Cybersecurity is not a one-time project but an ongoing business process. The objective is not to build an impenetrable fortress—an impossible goal—but to manage risk intelligently. A proactive approach involves understanding specific vulnerabilities and implementing a clear, prioritized plan to address them.
A well-defined cybersecurity strategy is not a cost center; it's a competitive advantage. It demonstrates to clients, partners, and insurers that you are a responsible steward of their data and a resilient organization.
This guide provides a clear roadmap to take control of your digital security. We will break down the essential steps, from foundational controls to employee training, to help you build a more resilient and secure business.
Layering Foundational Cybersecurity Controls

After identifying your key risks, the next step is to build your defenses. Effective cybersecurity for a small business is not about acquiring every available security tool. It is about systematically layering practical, high-impact controls that mitigate the most common attack vectors.
These foundational controls are non-negotiable. They serve as your first and most critical line of defense against threats that cause downtime, data loss, and significant financial damage.
Identity and Access Management
The traditional concept of a secure network "perimeter" is obsolete. Today, the perimeter is defined by user identity. Controlling who can access your data is one of the most critical security functions, which is why Identity and Access Management (IAM) must be your starting point.
The goal is to ensure only authorized individuals can access company resources—and only the specific resources required for their roles. Weak or stolen passwords remain a primary entry point for attackers.
Your security is only as strong as your weakest password. Multi-factor authentication is one of the single most effective controls you can implement, reducing the risk of a breach from credential theft by over 99%.
Implementing strong IAM involves two key components:
- Multi-Factor Authentication (MFA): This is essential. MFA requires a second form of verification, such as a code from a mobile app, before granting access. Even if a password is stolen, the attacker is stopped without this second factor.
- Strong Password Policies: Enforce standards for password length and complexity. More importantly, educate your team on the risks of password reuse and encourage the use of a secure password manager.
Endpoint Protection
Every laptop, desktop, server, and smartphone connected to your network is an endpoint—and a potential entry point for malware or ransomware. Protecting these devices is a fundamental requirement.
Modern endpoint protection goes beyond traditional antivirus software. Advanced solutions use behavioral analysis and machine learning to detect and block previously unknown threats. This security layer is vital for protecting your business wherever your team works, ensuring an employee in a coffee shop has the same level of security as one in the office.
Network Security Fundamentals
Your network is the digital backbone of your business. Proper security involves preventing unauthorized users from accessing internal systems and sensitive data. This requires more than a standard router.
A properly configured firewall acts as a gatekeeper, inspecting all incoming and outgoing traffic and blocking suspicious activity. It creates a critical barrier between your trusted internal network and the public internet. Secure Wi-Fi is also essential, requiring strong encryption (WPA3 is the current standard) and a separate guest network to isolate visitor traffic from core business systems. Following established network security best practices is the best way to ensure your digital infrastructure is secure.
Data Backup and Recovery
No security measure is 100% infallible. When an incident occurs—whether from a ransomware attack, hardware failure, or human error—a reliable backup and recovery plan is your ultimate safety net. It is what enables a swift return to operations, minimizing damage.
A resilient backup strategy adheres to the 3-2-1 rule:
- Maintain three copies of your data.
- Store them on two different types of media.
- Keep at least one copy off-site or in the cloud.
This redundancy is critical. If a ransomware attack encrypts both your primary data and local backups, a clean, isolated off-site copy allows for restoration. Remember, an untested backup is only a guess. Regular testing is required to confirm that your recovery process works as expected.
Essential Cybersecurity Controls for Small Businesses
| Control Area | Core Technology or Policy | Business Risk Mitigated |
|---|---|---|
| Identity Management | Multi-Factor Authentication (MFA) | Unauthorized account access, data breaches from stolen credentials |
| Endpoint Protection | Next-Generation Antivirus (NGAV) | Malware, ransomware, and spyware infections on company devices |
| Network Security | Firewall, Secure Wi-Fi Configuration | Network intrusion, data interception, unauthorized system access |
| Data Backup & Recovery | 3-2-1 Backup Rule, Regular Restore Tests | Data loss from ransomware, hardware failure, or accidental deletion |
Implementing these four foundational controls creates a layered defense that dramatically improves your security posture. By addressing identity, devices, your network, and data resilience, you build the solid foundation for a mature and effective security program.
Securing Your Microsoft 365 and SharePoint Data

For most businesses, Microsoft 365 is the operational hub where client emails, financial models, and sensitive contracts are stored in Outlook, SharePoint, and OneDrive. This centralization improves productivity but also creates a high-value target for attackers.
Securing this environment requires a deliberate strategy that goes beyond basic passwords. It involves configuring the powerful, built-in security tools that many businesses overlook. Protecting this core asset is a critical component of any effective cybersecurity for small business plan. The goal is to ensure your data remains confidential, intact, and accessible only to authorized users, mitigating risks that could lead to significant operational and financial damage.
Moving Beyond Default Security Settings
Microsoft 365 provides a reasonable security baseline, but relying on default settings is a common and costly error. To adequately protect your organization, you must fine-tune these controls to align with your specific risks and operational needs. This means shifting from a passive to an active security posture by making immediate, high-impact improvements that enforce policies automatically and reduce human error.
Implementing Conditional Access Policies
Conditional Access is one of the most powerful security tools available in Microsoft 365. It functions as an intelligent gatekeeper for your data, evaluating multiple signals before granting access.
These policies analyze signals to make automated, real-time decisions. For example, a policy can evaluate:
- User Location: Is the sign-in originating from a trusted country or an unusual location?
- Device Health: Is the device compliant with security policies, with up-to-date antivirus software?
- Application: Is the user attempting to access a highly sensitive resource, such as your primary SharePoint site for client files?
Based on these signals, you can grant access, require multi-factor authentication, or block the attempt entirely. This prevents a compromised but legitimate account from being used to access sensitive files from an untrusted network.
Preventing Data Leaks with DLP
Data Loss Prevention (DLP) adds another essential security layer. DLP policies act as a digital guard, identifying confidential data and preventing it from leaving your organization inappropriately.
You can configure policies that automatically recognize specific information types, such as:
- Financial data like credit card or bank account numbers
- Personally Identifiable Information (PII)
- Sensitive legal documents or health records
If a user attempts to email a document containing this information to an external address or save it to an unauthorized cloud service, the DLP policy can block the action and notify an administrator. It serves as a crucial safeguard against both accidental mistakes and malicious data exfiltration.
Effective governance in Microsoft 365 establishes a clear framework of rules and policies that protect data without impeding productivity. It is the digital equivalent of knowing who has keys to which filing cabinets and what they are permitted to do with the files inside.
Mastering Permissions and Governance
The principle of least privilege is a cornerstone of sound security. It means granting individuals access only to the information they absolutely need to perform their job. In SharePoint and Teams, this is achieved through diligent permissions governance.
Unmanaged permissions represent a significant hidden risk. As employees change roles or projects conclude, their access rights often remain, a phenomenon known as "permission creep." This can lead to a junior employee retaining access to sensitive executive-level files.
A proper governance plan includes:
- Regular Access Reviews: Periodically auditing who has access to what, especially for critical SharePoint sites.
- Clear Ownership: Assigning business owners to data who are responsible for approving access requests.
- Using Security Groups: Managing permissions via groups rather than individual accounts to simplify administration and reduce errors.
For a deeper analysis of protecting your entire infrastructure, our guide on advanced cybersecurity frameworks offers valuable insights. By implementing these specific controls within Microsoft 365, you can transform it from a productivity suite into a securely managed environment that safeguards your company's most valuable digital assets.
Building Resilience Through Monitoring and Incident Response
Even with strong defenses, a determined attacker may eventually succeed. At this point, your cybersecurity strategy must shift from prevention to resilience. Business continuity depends not only on building high walls but also on knowing precisely what to do when a breach occurs. Resilience is the ability to detect threats quickly and respond in a calm, structured manner to contain the damage.
Proactive Monitoring: You Can’t Fight What You Can’t See
You cannot respond to a threat you are unaware of. Proactive threat monitoring provides the necessary visibility to detect suspicious activity before it escalates into a crisis. This involves actively searching for subtle indicators of compromise rather than waiting for an alarm.
Modern monitoring tools offer a continuous, real-time view of your network, servers, and cloud services. They are designed to identify anomalies that could signal an attack, such as:
- Unusual login attempts from unexpected geographic locations.
- Large volumes of data being downloaded or transferred at odd hours.
- A user account attempting to access sensitive files for the first time.
Early detection shortens the time an attacker has within your systems, which is critical for containing an incident and preventing widespread damage.
The Critical Role of an Incident Response Plan
When a breach is confirmed, time is of the essence. Panic and confusion work to an attacker's advantage. A documented Incident Response Plan (IRP) is an operational necessity.
An IRP is your company’s playbook for a cyber crisis. It is a step-by-step guide that eliminates guesswork and ensures a coordinated, effective response. It clearly defines roles, responsibilities, and the specific actions to be taken from detection to full recovery.
A well-rehearsed Incident Response Plan transforms a chaotic, high-stress event into a structured, manageable process. It is the difference between making panicked decisions that worsen the situation and executing a calm, confident recovery that protects your assets and reputation.
A solid IRP covers several key phases to ensure a comprehensive response. You can begin building your own by using this detailed incident response plan template designed to guide businesses through the process.
Anatomy of an Effective IRP
A robust plan must be clear, concise, and actionable. It should outline precisely what to do during a security event.
Key Components of an Incident Response Plan:
- Preparation: This phase involves training the response team, implementing the necessary tools, and ensuring everyone understands their roles before an incident occurs.
- Identification: This is the process of confirming a security breach, determining its scope, and assessing its potential business impact.
- Containment: The immediate priority is to isolate affected systems to prevent the threat from spreading across the network. This may involve taking a server offline or disabling a user account.
- Eradication: Once contained, the threat must be completely removed. This includes eliminating malware, patching vulnerabilities, and ensuring the attacker cannot regain access.
- Recovery: This phase focuses on restoring affected systems and data from clean backups, verifying their security, and bringing them back online to resume normal operations.
- Lessons Learned: A post-incident review is crucial for understanding what went wrong, what went right, and how to strengthen both defenses and the response plan for the future.
For example, a law firm discovers ransomware has encrypted all client files. Without a plan, chaos ensues. With an IRP, the team calmly isolates the infected network, notifies stakeholders with a pre-approved script, and begins restoring data from tested, off-site backups. The difference in outcome is stark: one leads to prolonged downtime and reputational ruin, while the other results in a swift, controlled recovery.
Turning Your Team Into a Security Asset
While technology forms the foundation of your defense, your employees represent the true front line. The human element is the most frequently targeted aspect of any organization, making it a critical component of a realistic cybersecurity for small business strategy.
The goal is not to assign blame but to empower your team. By cultivating a strong, security-conscious culture, you can transform your employees from a potential vulnerability into a proactive security asset where everyone understands their role in protecting the company.
Building a Human Firewall
An effective cyber-awareness program is more than a once-a-year training video. It is a continuous effort to keep security top of mind and integrate safe practices into daily routines. A mature program combines several key components to create a resilient "human firewall."
This approach directly addresses the most common human errors, such as clicking malicious links in phishing emails or reusing weak passwords. By equipping staff with practical knowledge, you give them the confidence to identify and report threats before they can cause damage. Robust employee cybersecurity training is absolutely essential for building a strong defense.
Components of an Effective Program
A successful security awareness initiative is an ongoing process, not a single event. To be effective, training must be practical, engaging, and relevant to the threats employees face daily.
- Continuous Education: Regular, bite-sized training keeps security concepts fresh. Short monthly videos or security tips in a company newsletter are more effective than a long annual presentation.
- Realistic Phishing Simulations: The best way to train people to spot phishing attacks is through safe, practical experience. Sending simulated phishing emails helps employees learn to identify red flags without exposing the business to real risk.
- Clear and Simple Policies: Security policies must be easy to understand and follow. Focus on clear, concise guidance for critical areas like password creation, data handling, and reporting suspicious activity.
A well-trained team acts as a powerful extension of your security systems. When an employee confidently reports a suspicious email instead of clicking on it, they have neutralized a threat that technology might have missed.
Training as a Compliance Tool
Beyond the security benefits, a documented training program is a vital tool for meeting regulatory compliance obligations. Many data privacy laws, such as the California Consumer Privacy Act (CCPA), require organizations to prove they are actively training staff on security and data protection. Documenting your training efforts provides concrete evidence that you take data protection seriously, which can significantly reduce legal and financial exposure in the event of an audit or breach.
Investing in your people is one of the highest-return activities in cybersecurity. For a deeper look into structuring these initiatives, see our guide on cybersecurity training for employees. A security-aware culture not only reduces risk but also builds a more resilient and responsible organization from within.
Defining Your Strategic Cybersecurity Roadmap
We have covered risk assessments, essential controls, Microsoft 365 security, and incident response. Now it is time to integrate these elements into a clear, practical roadmap that translates strategy into action.
This roadmap should function as a business plan for managing cyber risk, focused on setting priorities, allocating resources, and establishing realistic timelines. A well-structured plan moves your organization from a reactive mode to a proactive posture, ensuring security efforts directly support your business goals.
Budgeting for Resilience
Budgeting is a common challenge for small businesses. Data shows that 74% of small businesses allocate less than 10% of their total budget to cybersecurity. However, this spending should be viewed as an investment in business continuity, not just an expense. The cost of a major breach—in downtime, lost client trust, and recovery fees—will always exceed the cost of proactive protection.
Your budget should directly reflect your risk assessment, prioritizing the most significant risks first.
- Foundational Controls: Begin with multi-factor authentication (MFA), endpoint protection, and a solid backup strategy. These deliver the greatest risk reduction for the investment.
- Platform Security: If your business relies on Microsoft 365, properly configuring its advanced security features is non-negotiable.
- Training: Security awareness programs are highly cost-effective, transforming your employees from a potential liability into a powerful defensive asset.
An effective employee security program relies on a continuous improvement cycle.
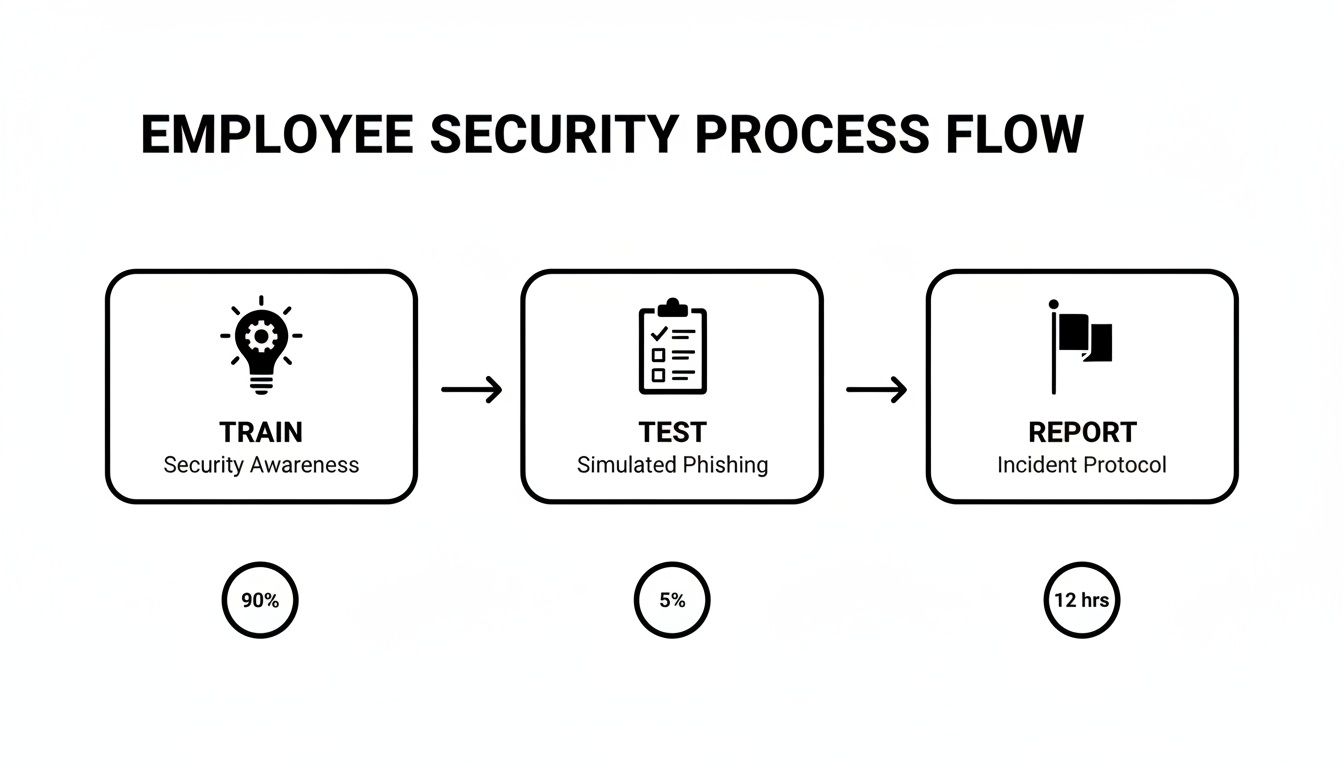
This process illustrates the ideal loop: train your team, test their awareness with simulations, and make it easy to report suspicious activity. This constant reinforcement builds a genuine security-first culture.
Timelines and Implementation
Attempting to implement everything at once is counterproductive. A practical cybersecurity roadmap should be phased, allowing you to introduce changes methodically without overwhelming your team or disrupting operations. A quarterly plan is often the most effective approach.
A Sample 12-Month Roadmap:
| Quarter | Primary Focus | Key Actions |
|---|---|---|
| Q1 | Foundational Controls | Deploy MFA company-wide, implement advanced endpoint protection, verify 3-2-1 backup strategy. |
| Q2 | Platform Hardening | Conduct Microsoft 365 security audit, implement Conditional Access and DLP policies. |
| Q3 | Resilience & Training | Develop and test Incident Response Plan, launch phishing simulation program. |
| Q4 | Review & Refine | Conduct annual risk assessment, review access permissions, plan next year's priorities. |
A structured timeline transforms a large initiative into a series of manageable projects. The key is to maintain momentum, as cybersecurity is an ongoing process, not a one-time task. For businesses with more complex needs, you can learn more about how to safeguard your business's most sensitive data using advanced frameworks.
Internal Team vs. Managed Partner
A key strategic decision is whether to manage cybersecurity in-house or partner with a managed security provider. For most small and mid-sized businesses, the complexity and need for constant vigilance make a purely internal approach both impractical and costly.
An experienced managed IT and cybersecurity partner provides access to enterprise-grade tools and specialized expertise that would be prohibitively expensive to build internally. This model offers predictable costs and allows your team to focus on core business operations.
A Virtual CIO (vCIO) or Fractional CIO can provide the high-level strategic guidance needed to build your roadmap, justify budgets, and make informed technology decisions without the expense of a full-time executive. They serve as a bridge between your business objectives and the technical execution required to achieve them securely.
A well-defined roadmap transforms cybersecurity from an intimidating threat into a clear path forward. By setting smart priorities, budgeting intelligently, and leveraging expert guidance, you can build a resilient organization prepared for future challenges. To discuss building a security roadmap that fits your unique business needs, contact the experts at Tricord I.T Solutions.

