IT infrastructure management services involve the professional oversight of a company's core technology foundation, including its network, servers, data storage, and security systems. The primary goal is to ensure these components are reliable, secure, and cost-effective, allowing business leaders to focus on strategic objectives rather than day-to-day technical issues.
For business owners and executives, this means partnering with a provider to manage the technology that powers daily operations. This proactive approach aims to prevent disruptions, control costs, and reduce business risk associated with downtime, data loss, or cyber threats. A well-managed infrastructure supports stable operations today and provides a scalable foundation for future growth.
Understanding the Value of IT Infrastructure Management
Think of your IT infrastructure as the central nervous system of your business. It is the engine powering daily communications, data access, and the critical applications that drive revenue and operations. Like any complex system, it requires constant attention, maintenance, and strategic planning to perform optimally. Poorly managed infrastructure creates significant business risks, from crippling downtime and data breaches to uncontrolled spending.
This is where professional it infrastructure management services provide value. They act as expert custodians for this vital system. Their role extends beyond fixing issues as they arise; it is a proactive discipline designed to prevent problems from disrupting your operations. This ensures your technology not only supports current business activities but is also prepared to scale with you.
A High-Level View of Key Components
Effective management is not a single task but a combination of several interconnected technology disciplines. Each component plays a critical role in your company's operational stability and security. Understanding these components clarifies where a managed services partner can deliver tangible business value.
For business leaders, recognizing these functions is key to understanding how integrated IT management directly enhances productivity and mitigates risk. The table below outlines the core components and their business impact, offering a quick reference for executives evaluating their technology needs.
Core Components of IT Infrastructure Management
| Component | Its Role in Your Business Operations |
|---|---|
| Network Management | Ensures secure and reliable connectivity for your team, providing seamless access to critical applications and data. |
| Server Administration | Manages the physical and virtual servers that run your applications, ensuring high performance and availability. |
| Data Storage and Backups | Protects your company’s most valuable asset—its information—from loss or corruption with structured storage and robust recovery plans. |
| Security and Compliance | Implements and maintains firewalls, threat monitoring, and other safeguards to defend against cyber threats and meet regulatory requirements. |
| Proactive Monitoring | Provides 24/7 oversight of your entire infrastructure to identify and resolve potential issues before they cause downtime or data loss. |
By entrusting these responsibilities to a specialized partner, businesses gain access to expertise and technology that would otherwise be cost-prohibitive. It is a strategic decision that helps control costs, reduce operational risk, and build a more resilient and efficient technology foundation.
Understanding Your Core Technology Infrastructure
To manage your technology effectively, you first need a clear understanding of its components. Your IT infrastructure is more than just computers; it is the interconnected system of hardware and software that powers your entire business. Recognizing these core pillars is the first step toward reducing risk and improving performance.
Each component plays a distinct role. If one is mismanaged, it can cause significant disruptions that impact your entire operation. Let's break down the four essential pillars of a modern business's technology foundation.
The Network: Your Digital Nervous System
Your network is the digital nervous system connecting your team, data, and customers. It includes everything from Wi-Fi access points and office cabling to the firewalls and switches that direct traffic and maintain security. When it functions correctly, it is invisible. When it fails, business operations can grind to a halt.
A poorly managed network is a direct threat to productivity. Common symptoms include slow applications, dropped video calls, and unreliable access to shared files—all of which frustrate employees and impede operations. More critically, a network with security gaps is an open invitation for cyber threats, putting sensitive company and client data at risk.
Effective network management ensures data flows quickly and securely. This involves configuring hardware for optimal performance, monitoring for suspicious activity, and ensuring the system can handle your company’s workload without bottlenecks. This proactive oversight keeps your team connected and your data safe.
Servers: The Brains of Your Operations
Servers are the powerful computers that run your essential business applications, host your website, and manage your company data. Whether they are physical machines in an office or virtual servers in the cloud, they are the central processing unit of your business.
A server failure can be catastrophic, leading to immediate and widespread downtime. If the server running your primary business software goes offline, your entire team may be unable to work. This not only impacts productivity but can also damage your reputation if it affects customer-facing services. Effective IT Asset Management services are often part of a broader infrastructure strategy, ensuring every piece of technology is tracked, optimized, and managed throughout its lifecycle.
A well-managed server environment prioritizes stability and performance. It requires constant monitoring of system health and resources, prompt security patching to close vulnerabilities, and strategic capacity planning to ensure your servers can support business growth.
Regular maintenance is crucial for preventing unexpected failures that cause operational chaos. You can see how we approach this with our managed infrastructure services, which are built around proactive care.
Storage: Your Company’s Memory
Your data storage systems serve as the memory of your organization. This is where all critical information resides—from client records and financial documents to intellectual property and operational files. Storage can be located on local servers, dedicated network devices, or cloud platforms like Microsoft 365.
The primary risks here are data loss and unauthorized access. Without proper management, files can be accidentally deleted, become corrupted, or be accessed by unauthorized individuals. Furthermore, disorganized storage makes it difficult for teams to find necessary information, creating hidden inefficiencies that drain productivity.
Proper storage management involves more than just providing a place to save files. It requires:
- Organized Structure: Building a logical file system so information is easy to find and access.
- Access Controls: Implementing permissions to ensure only authorized personnel can view or modify sensitive data.
- Performance Optimization: Ensuring the storage system is fast enough to meet business demands without causing delays.
Backup Systems: Your Insurance Policy
If storage is your company’s memory, then your backup system is its insurance policy. Backups are copies of your critical data stored in a separate, secure location. They are your last line of defense against data loss resulting from hardware failure, ransomware attacks, human error, or physical disasters.
The consequences of having inadequate or non-existent backups are severe. A major data loss event without a reliable backup can threaten a company's survival. Many businesses rely on outdated or untested backup methods, creating a false sense of security. They often discover their backups are ineffective only during a crisis.
A robust backup strategy is non-negotiable for business continuity. This involves:
- Regular, Automated Backups: Ensuring data is copied consistently without manual intervention.
- Secure, Offsite Storage: Keeping copies in a different physical or cloud location to protect against local disasters.
- Regular Testing: Periodically performing test restores to confirm that backups are working and can be recovered quickly.
Each of these four pillars—network, servers, storage, and backups—is essential for a stable and secure technology foundation. Managing them effectively is a fundamental business requirement for operational continuity and risk mitigation.
Finding the Right Service Model for Your Business
Choosing how to manage your IT infrastructure is a significant business decision. The best approach depends on your company’s size, in-house capabilities, and strategic goals. There is no one-size-fits-all solution; the objective is to find a model that aligns with your operational needs and long-term vision.
The first step is to understand the primary delivery models. Each offers a different level of involvement, cost structure, and responsibility, tailored to specific business scenarios.
This decision tree provides a simplified framework for evaluating your core infrastructure needs.
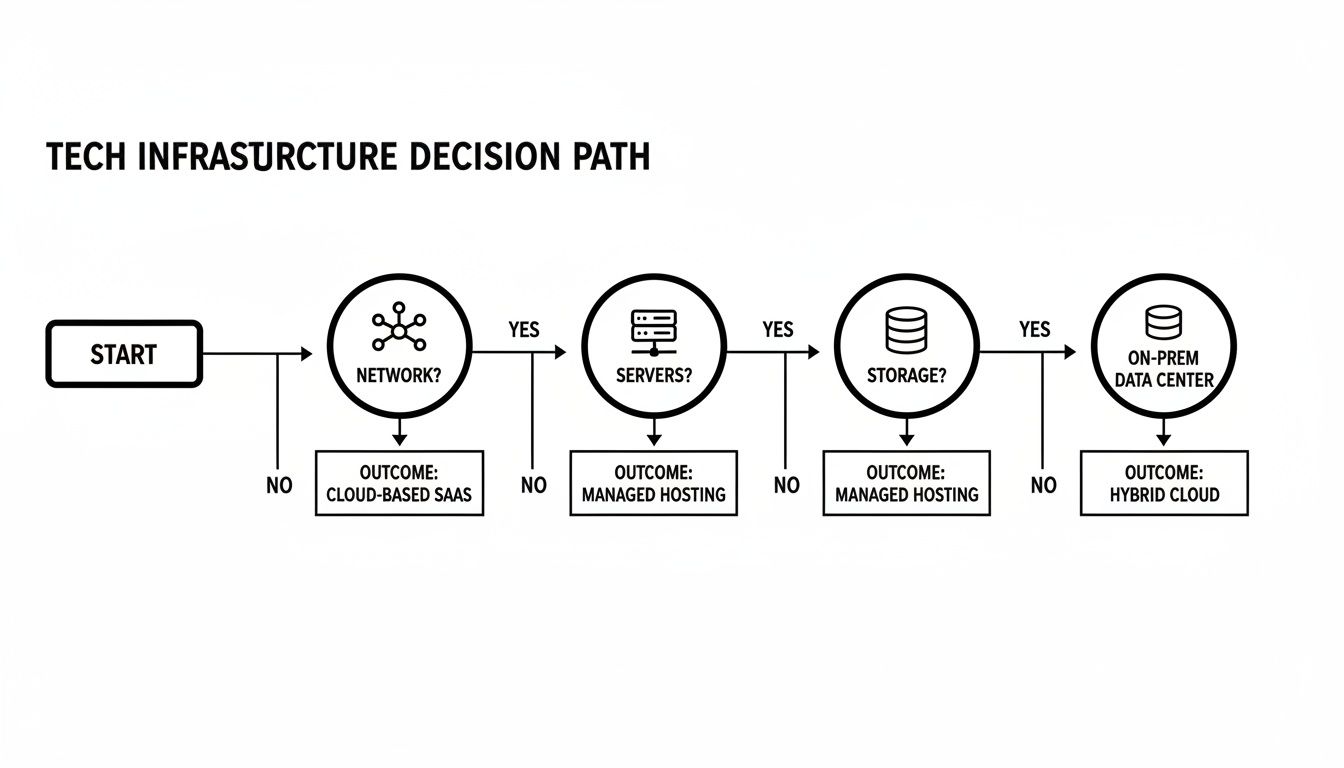
Visualizing the connections between networks, servers, and storage helps clarify which management strategy is the right fit for your business.
Fully-Managed Services
The fully-managed model is equivalent to outsourcing your entire IT department. A third-party provider assumes full responsibility for everything from daily help desk support and proactive maintenance to long-term strategic planning and security monitoring.
This model is an excellent fit for:
- Small to midsize businesses without the budget or need for a full-time, in-house IT team.
- Companies seeking to control costs by converting unpredictable IT capital expenditures into a stable, predictable monthly operational expense.
- Businesses in regulated industries that require specialized security and compliance expertise they lack internally.
With a fully-managed partner, you gain access to a team of experts and advanced technology that would be too expensive to develop in-house. To learn more about this approach, you can explore what is managed IT services in our detailed guide.
Co-Managed IT Services
Co-managed IT is a hybrid model—a strategic partnership between your existing IT team and an external provider. It is designed to augment your internal staff, not replace them. Your team can focus on daily user support and business-specific applications, while the managed services provider (MSP) delivers specialized tools, 24/7 monitoring, and high-level expertise for complex projects or security management.
This collaborative model empowers your internal team by offloading time-consuming maintenance and monitoring, freeing them to focus on strategic, business-aligned projects that drive growth.
A co-managed partnership is ideal for:
- Companies with a small internal IT department that is stretched thin and struggling to balance daily demands with strategic initiatives.
- Organizations that need specialized skills in areas like cybersecurity, cloud migration, or compliance that their current team does not possess.
- Businesses that want to retain their internal IT staff for their institutional knowledge while gaining the resources of a larger, specialized firm.
The Caribbean data center market is experiencing significant investment in IT infrastructure, with global technology firms expanding their presence. As of 2022, the market included 15 third-party facilities, with more planned. This growing infrastructure enables robust managed services, providing organizations with essential hosting and operational support.
Virtual CIO (vCIO) Services
Virtual CIO (vCIO) services provide high-level strategic guidance without the cost of a full-time executive. A vCIO acts as your senior technology advisor, focused on aligning your IT infrastructure with your core business goals. They do not handle daily tech support; their role is centered on long-term planning, budgeting, risk management, and ensuring your technology investments deliver a positive return.
This model is a perfect match for:
- Growing businesses that need strategic IT leadership but are not large enough to justify a full-time CIO salary.
- Organizations planning major technology initiatives, such as a cloud migration, that require expert guidance to ensure a successful project.
- Leadership teams seeking an unbiased, expert perspective on technology decisions, risks, and opportunities.
A vCIO provides the technology roadmap, helping you make smarter, more cost-effective decisions that support sustainable growth and maintain a competitive advantage.
Integrating Security and Compliance into Your Infrastructure

In the modern business environment, managing technology and managing business risk are inextricably linked. A contemporary approach to it infrastructure management services integrates security and compliance into the foundation of your technology, rather than treating them as add-ons. This is essential for protecting sensitive data, maintaining client trust, and ensuring operational continuity.
An experienced IT partner works to embed security into every layer of your infrastructure. This forward-thinking strategy goes beyond simple antivirus software, creating a multi-layered defense designed to mitigate business risk from all angles. It is about building a resilient organization from the ground up.
Building a Proactive Defence System
Effective security is not a one-time setup; it is a continuous process of management and monitoring. A managed services provider implements and actively manages the essential security controls that protect your data and systems against an ever-changing threat landscape.
This involves several key activities working in concert to create a strong defensive posture. These controls are your front-line defense against unauthorized access, data breaches, and operational disruptions.
Core security management activities include:
- Firewall Management: Configuring and monitoring your firewalls to control network traffic and block malicious connections before they reach your internal systems.
- Endpoint Protection: Deploying and managing advanced security software on all devices—from computers to servers—to detect and neutralize malware and ransomware.
- Proactive Threat Monitoring: Using sophisticated tools to provide 24/7 surveillance of your network, identifying and responding to suspicious activity in real-time.
A proactive approach to protecting your infrastructure also includes regular assessments, such as a computer network security audit, to identify potential vulnerabilities. This process ensures your defenses remain aligned with current security best practices.
Navigating Complex Compliance Requirements
For businesses in regulated industries such as law, healthcare, or finance, adhering to compliance standards is mandatory. Navigating frameworks like PIPEDA or other industry-specific regulations can be challenging, demanding specialized knowledge and meticulous attention to detail.
A key benefit of professional IT management is the ability to transform these complex requirements into a structured, manageable process. The right partner acts as your compliance guide, helping you implement the necessary technical controls and generate the documentation required for audits.
By translating dense regulatory language into practical IT policies and procedures, a managed services provider demystifies compliance. They help ensure your infrastructure is configured to meet specific legal and industry mandates, reducing the risk of costly fines and reputational damage.
This strategic support removes a significant administrative burden from your team, allowing them to focus on core responsibilities instead of becoming compliance experts.
Integrating Security into Daily Operations
True infrastructure security extends beyond technology to include the daily habits of your team. A holistic management strategy involves educating users on how to recognize phishing attempts and handle sensitive data responsibly. This combination of technology, policy, and education creates a genuinely secure environment. To learn more about this layered approach, you can read about the benefits of implementing advanced cybersecurity frameworks in our detailed article.
Ultimately, integrating security and compliance is about building resilience. When these principles are embedded into the core of your IT infrastructure, you not only protect your assets but also build trust with clients and partners. It demonstrates a commitment to operational excellence and responsible data stewardship—a powerful competitive advantage.
The Strategic ROI of Professional IT Management
Evaluating IT infrastructure management services is not just a technical consideration—it is a financial and strategic decision. For any business leader, the central question is: how does this investment improve efficiency, reduce risk, and prepare us for growth? A professional IT partner transforms your technology from a budget line item into a strategic asset that drives business forward.
One of the most immediate financial benefits is the shift from unpredictable capital expenditures (CapEx) to a stable, manageable operating expense (OpEx). Instead of facing large, unexpected bills for new servers or critical software upgrades, you have a predictable monthly cost. This simplifies budgeting and frees up capital for revenue-generating initiatives.
Maximizing Uptime and Productivity
Downtime directly impacts your revenue and reputation. Every minute your systems are offline, your team cannot work, and your clients cannot access your services. Professional IT management is built on the principle of preventing problems before they occur.
This proactive approach is a game-changer. It dramatically reduces the frequency and impact of technical issues. By identifying and resolving potential problems early—such as a failing hard drive or a slow network—a managed services partner ensures your team has the reliable tools they need to remain productive.
Enhancing Security and Reducing Risk
The consequences of a single security breach can be severe, leading to regulatory fines, legal liabilities, and lasting brand damage. Professional IT management provides a critical layer of defense, implementing robust security protocols that most small and mid-sized businesses cannot build or maintain on their own.
Investing in proactive infrastructure management is fundamentally an investment in business resilience. It fortifies your operations against technical failures and cyber threats, ensuring your organization can withstand disruptions and maintain client trust.
This goes beyond firewalls to include endpoint protection, continuous threat monitoring, and access to security specialists. Entrusting your security to experts immediately lowers your risk profile and demonstrates to clients and regulators that you take data protection seriously.
Focusing on Core Business Objectives
Perhaps the most significant return is strategic. When your key employees are constantly diverted to address IT emergencies, they are not focused on the work that grows the business. Offloading the daily management of infrastructure frees your team to concentrate on innovation, process improvement, and achieving strategic goals.
Consider the growth of e-commerce, which requires businesses to have faster, more reliable networks. As shown by network infrastructure trends on statista.com, this demand is increasing. An IT partner manages the underlying technology to ensure it performs reliably, allowing your team to focus on enhancing the customer experience and pursuing new market opportunities. This alignment is where professional IT management delivers its true value, turning technology into a competitive advantage.
How to Choose the Right IT Management Partner

Selecting a partner to manage your core technology is a critical business decision. The right partner becomes a strategic asset that enhances efficiency and reduces risk. The wrong one can lead to operational friction, increased vulnerability, and frustration.
This decision should not be based on price alone. It requires a structured framework for evaluating potential providers of IT infrastructure management services. The goal is to look beyond the sales presentation to understand their operational processes, success metrics, and long-term support model.
Evaluating Technical Expertise and Industry Knowledge
Technical proficiency is the baseline requirement. What distinguishes a good partner from a great one is a genuine understanding of your industry. A firm with experience in legal, healthcare, or manufacturing will already be familiar with your specific operational challenges and compliance obligations.
When vetting potential partners, ask specific questions:
- Industry Experience: Have they worked with businesses in your sector? Request case studies or client references.
- Core Competencies: Do they have certified professionals for the technologies you rely on, such as Microsoft 365 and SharePoint?
- Team Structure: Who will be your primary point of contact? What is the depth of their technical team?
Understanding Service Level Agreements
A Service Level Agreement (SLA) is the blueprint for your partnership. It defines the provider's commitments for system uptime, response times, and issue resolution. A vague or weak SLA is a significant red flag.
A clear, comprehensive SLA is your guarantee of service quality. It should provide specific, measurable metrics for performance, ensuring accountability and setting clear expectations from day one.
Look for an SLA that details response times for critical, high, medium, and low-priority issues. It should also specify performance guarantees and the remedies if those guarantees are not met. This level of detail demonstrates a commitment to service quality and transparency.
Verifying Security and Compliance Credentials
As cyber threats become more sophisticated, your provider’s security posture is non-negotiable. You are entrusting them with your most sensitive data, so their security and compliance record must be impeccable.
Ask for evidence of their internal security controls. Inquire about their approach to cybersecurity services and ask about certifications, such as SOC 2, or their experience with industry-specific regulations. A mature provider will not only welcome these questions but will also have documentation ready to support their claims.
Making the right choice requires due diligence, but this structured approach will help you find a partner truly invested in your success.
Frequently Asked Questions About IT Infrastructure Management
Business leaders often have practical questions when considering a professional IT management partner. Here are straightforward answers to the questions we hear most often.
What Is the Difference Between Managed Services and Break-Fix IT Support?
The primary difference is the approach: proactive versus reactive. Break-fix support is a traditional model where you call for help only after something has broken. This reactive approach often leads to more downtime and unpredictable costs, as you are constantly paying for emergency repairs rather than preventative maintenance.
IT infrastructure management services, in contrast, are based on a proactive, subscription-based model. Your provider continuously monitors your systems to identify and resolve potential issues before they can disrupt your business. This aligns the provider's success with your operational stability—they succeed when your technology runs smoothly, not when it fails.
What Does the Onboarding and Transition Process Look Like?
A successful transition depends on a structured onboarding process. It typically begins with a thorough discovery phase, where the new provider audits your existing infrastructure, documents all systems, and identifies any security vulnerabilities or performance issues.
Following the audit, they will deploy their monitoring tools and begin stabilizing and securing the environment. A quality partner will work closely with your team to ensure a seamless handover, providing clear communication throughout the process to avoid surprises.
The goal of professional onboarding is not to simply flip a switch. It is a carefully planned project designed to transition you from your current state to a stable, secure, and fully managed environment without disrupting daily operations.
How Are IT Infrastructure Management Services Priced?
Pricing models are designed to create predictability, shifting your IT costs from unpredictable capital expenditures to a stable operating expense. The most common models include:
- Per-User Pricing: A flat monthly fee for each employee, typically covering all their devices and support needs.
- Per-Device Pricing: A fixed monthly cost for each managed device, such as a server, computer, or network switch.
- Tiered Packages: Bundled services offered at different levels (e.g., bronze, silver, gold), allowing you to select the package that best aligns with your needs and budget.
At Tricord I.T Solutions, we build a clear technology roadmap that aligns with your business goals, ensuring every investment in your infrastructure delivers measurable value. If you are ready to shift from a reactive to a proactive technology strategy, schedule a consultation with our team.

