A cybersecurity services company is a strategic partner dedicated to protecting your organization's digital assets, managing risk, and ensuring operational continuity. Unlike a simple software vendor, they provide a team of specialized experts who integrate security measures directly into your business strategy, freeing up leadership to focus on growth. For any modern business, but especially those in regulated industries like law, finance, or healthcare, partnering with the right firm is a critical decision.
The primary role of a cybersecurity services company is to move your organization from a reactive "break-fix" approach to a proactive, strategic security posture. They handle everything from 24/7 threat monitoring and compliance management to strategic guidance, ensuring your technology investments align with your business goals. This partnership helps minimize downtime, reduce the risk of costly data breaches, and maintain regulatory compliance, turning cybersecurity from an expense into a business enabler.
Understanding a Cybersecurity Company’s Business Value
An effective cybersecurity services company acts as an extension of your leadership team, weaving security directly into your strategic objectives. Their function is to translate technical controls into tangible business advantages, such as reduced risk, improved operational resilience, and strong compliance.
This partnership is essential for any modern business, but it's particularly critical for those in regulated fields like law, finance, and healthcare. In these sectors, a single security incident can lead to severe financial penalties, reputational damage, and loss of client trust. The right firm provides strategic guidance that protects the bottom line and supports long-term growth.
Core Functions and Business Impact
To understand the value these companies provide, it's helpful to review the diverse cyber security services they offer. A true partnership delivers measurable business benefits tied directly to their core functions.
This table breaks down the primary responsibilities a cybersecurity services company handles and the direct business value each function provides.
| Core Function | Business Impact |
|---|---|
| Risk Management | Proactively identifies and mitigates vulnerabilities, reducing the likelihood of a costly security incident and protecting your reputation. |
| Operational Continuity | Implements measures to ensure critical business processes remain functional during and after a disruption, minimizing downtime and revenue loss. |
| Compliance Adherence | Navigates complex industry regulations, helping the business avoid fines, penalties, and legal issues related to data protection. |
| Strategic Guidance | Provides expert advice on technology investments and security roadmaps, ensuring your security posture scales with your business. |
A common mistake is viewing cybersecurity through a purely technical lens. An effective partner understands that protecting patient data in a hospital is vital, but so are the systems managing appointments and emergency response. Protecting these operational dependencies is as critical as securing the data itself.
Ultimately, a cybersecurity services company integrates into your operations to build resilience from the ground up. They provide the expertise and infrastructure needed to defend against sophisticated threats, giving you the confidence to operate securely and grow without fear.
The Core Services Modern Cybersecurity Firms Provide
A cybersecurity services company delivers a suite of integrated services designed to protect your entire operation. These offerings are focused on proactive defense, strategic guidance, and rapid recovery. For business leaders, understanding these core functions is key to seeing how such a partnership translates directly into reduced risk and greater operational reliability.
The diagram below illustrates how a cybersecurity partner connects three critical pillars: managing risk, ensuring continuity, and maintaining compliance.
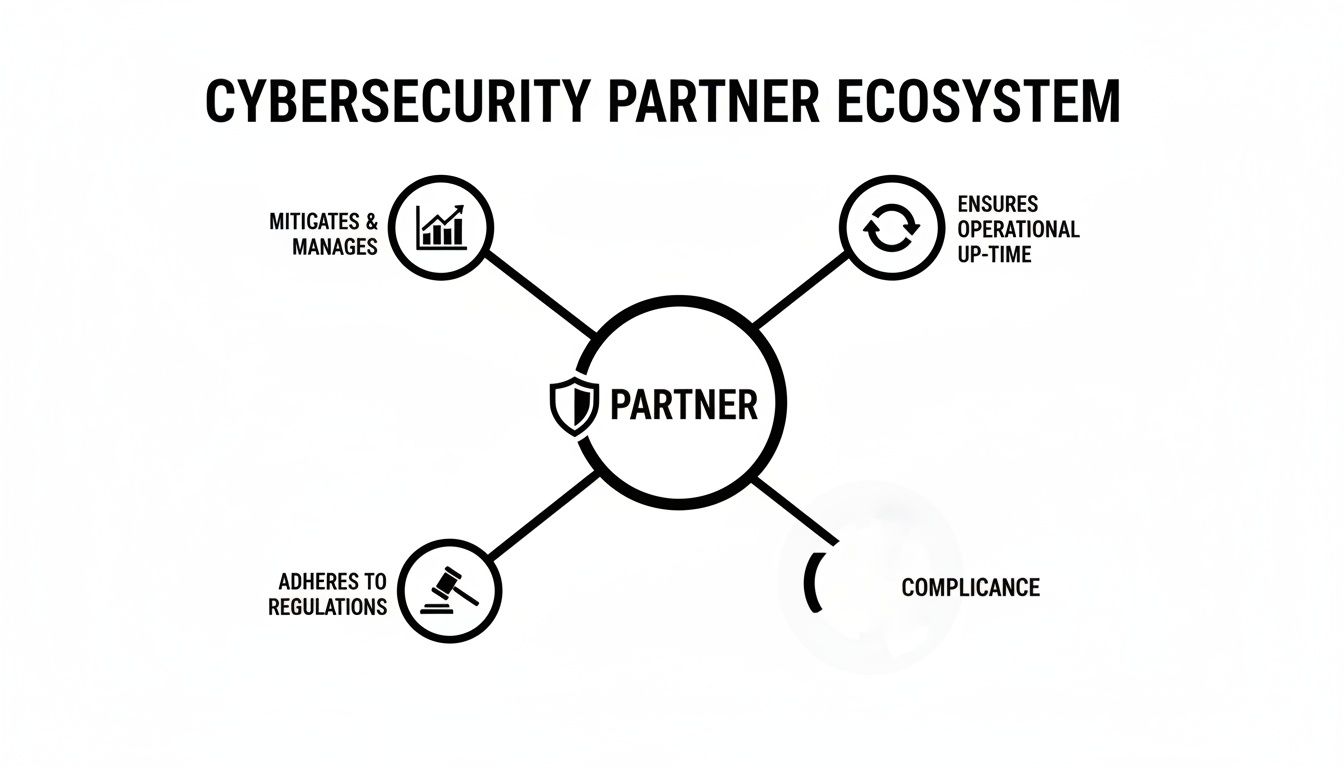
A partner’s value isn't just in the technology they deploy; it’s in how those defenses support fundamental business goals, creating a more resilient and compliant organization.
Managed Threat Monitoring and Response
At the core of modern cybersecurity is 24/7 Managed Threat Monitoring and Response, often called Managed Detection and Response (MDR). This service acts as a constant watchdog for your network, servers, and employee devices. Instead of waiting for an alarm, a team of security experts actively hunts for suspicious activity that could signal an impending attack.
Think of it as a high-tech security system for your business that includes not just cameras but also a dedicated team watching the feeds in real-time. If they spot an anomaly, they intervene immediately—long before a breach occurs. This proactive approach is essential because cyber threats do not operate on a 9-to-5 schedule.
Compliance Management and Reporting
For businesses in regulated industries like law, finance, or healthcare, adhering to strict data protection laws is mandatory. Compliance Management is a key service that involves implementing and documenting the specific technical and administrative controls required by regulations.
Your partner helps you navigate complex frameworks, ensuring your systems are configured to protect sensitive data according to legal standards. This service is crucial for avoiding the steep fines and reputational damage that result from non-compliance, providing peace of mind that your operations meet all necessary legal and industry requirements.
Virtual CIO Strategic Guidance
Many small and mid-sized businesses cannot afford a full-time Chief Information Officer (CIO). A Virtual CIO (vCIO) service fills this gap by offering executive-level strategic guidance without the executive-level salary. A vCIO works with your leadership team to develop a technology roadmap that aligns with your business goals.
A vCIO’s role is to ensure technology serves the business, not the other way around. They translate complex technical decisions into clear business impacts, helping you invest wisely in solutions that support growth, efficiency, and security.
This guidance helps prevent costly mistakes, such as investing in inappropriate technology or failing to plan for future growth. With a vCIO, you gain a strategic partner focused on your long-term success.
Incident Response Planning
Even with strong defenses, a security incident can still occur. How your organization responds in the first few hours can determine whether it's a minor disruption or a major catastrophe. Incident Response (IR) Planning is a service that prepares your business to act decisively and effectively when an incident happens.
Your cybersecurity partner will work with you to create a clear, actionable plan that outlines:
- Who to contact: Establishing a clear chain of command and communication.
- What steps to take: Detailing immediate technical and operational actions.
- How to recover: Creating a roadmap to restore systems and data safely.
A solid IR plan minimizes downtime, reduces financial losses, and ensures a coordinated response. Modern firms often implement a comprehensive approach to infrastructure protection, which can include layered security for data centers that covers physical, technical, and operational aspects. To see how this protection extends to individual devices, you can learn more about what endpoint detection and response is.
Employee Security Awareness Training
Technology alone cannot stop every threat. Many successful cyberattacks begin with a human error, such as an employee clicking a malicious link. This is why Employee Security Awareness Training is a critical component of a comprehensive security strategy.
A good partner provides ongoing training that teaches your team how to recognize phishing attempts, use strong passwords, and handle sensitive data securely. By transforming your employees from potential liabilities into a vigilant first line of defense, you significantly strengthen your organization’s overall security posture.
Why Regulated Industries Need Specialized Cybersecurity
For businesses in sectors like law, healthcare, and finance, cybersecurity is a core business function tied directly to regulatory compliance and client trust. These industries operate under strict rules governing privacy and confidentiality, making the consequences of a breach particularly severe.
A generic security plan is insufficient. The sensitive nature of the data—privileged client information, private health records, or financial data—raises the stakes. The risk of reputational damage, legal action, and significant fines is a constant reality. A specialized cybersecurity services company understands this and builds strategies where compliance is the foundation, not an afterthought.

Law Firms: Protecting Client Confidentiality
For a law firm, the entire client relationship is built on the absolute protection of privileged information. A data breach doesn't just leak sensitive case details; it shatters client trust and can lead to serious ethical violations. The mission is to secure every communication and document, especially those managed in platforms like Microsoft 365 and SharePoint.
An industry-aware cybersecurity partner implements controls designed for legal workflows, including:
- Granular access controls to ensure only authorized personnel can access sensitive case files.
- End-to-end data encryption to protect information in transit and at rest.
- Secure collaboration tools that allow for confidential communication without exposure.
A breach could expose legal strategies or settlement negotiations, jeopardizing case outcomes and the firm's reputation.
Healthcare: Safeguarding Patients and Ensuring Continuity
In healthcare, the mission is twofold: safeguard Protected Health Information (PHI) to comply with regulations like HIPAA and ensure clinical systems remain continuously available. A cyberattack on a clinic or hospital can have life-threatening consequences, disrupting everything from patient admissions to critical medical equipment.
A specialized provider understands that security must support clinical workflows, not hinder them. They focus on securing electronic health record (EHR) systems, protecting networked medical devices, and training staff to recognize threats that could compromise patient safety. The goal is to maintain both data privacy and operational resilience.
Finance: Securing Transactions and Client Assets
The financial sector is a primary target for cybercriminals due to the direct access to funds and valuable client data. For these organizations, security is about protecting transactions, preventing fraud, and navigating a complex web of financial regulations. Even a minor vulnerability can be exploited for significant financial gain.
A cybersecurity partner with financial industry expertise will prioritize:
- Transactional security to protect the integrity of transfers and client accounts.
- Advanced fraud detection systems to identify and stop suspicious activity in real-time.
- Continuous compliance audits to ensure alignment with industry standards.
The need for this specialized focus is amplified by regional threat trends. For example, recent data shows that in 2023-2024, government and financial sectors were heavily targeted by ransomware attacks. This trend highlights the urgent need for proactive threat monitoring and compliance management tailored to these high-risk industries.
For regulated businesses, compliance is the baseline, not the finish line. A true cybersecurity partner goes beyond regulatory checklists to build a resilient operational framework that protects your clients, your reputation, and your bottom line.
Choosing a cybersecurity services company that understands your industry's operational realities and regulatory burdens is a critical business decision. It ensures your security strategy is not just technically sound but also strategically aligned with your core mission.
Understanding the Shift to Managed Cybersecurity Services
For years, many businesses operated with a reactive IT support model. When something breaks, you call for help, and a technician arrives to fix the problem. This is the break-fix approach—it only addresses cybersecurity threats after the damage is done.
In today's environment, where a single breach can be catastrophic, waiting for something to go wrong is a failed strategy. The modern solution is a proactive partnership with a managed cybersecurity services company. This represents a complete shift in mindset—instead of paying to clean up a disaster, you invest in preventing it from happening in the first place.
The Problem with the Break-Fix Model
The break-fix model has a fundamental flaw: it creates a conflict of interest. A provider using this model is only paid when your systems are down. Their business model is built on your misfortune, not your operational stability.
This approach is also unpredictable. You are left guessing what the next emergency will cost in repairs, data recovery, and lost productivity, making effective budgeting nearly impossible. Worst of all, it leaves your business vulnerable, as it does nothing to stop sophisticated cyberattacks.
Advantages of the Managed Services Model
A managed services model reverses this dynamic. You pay a predictable, fixed monthly fee for continuous monitoring, maintenance, and defense. This simple change aligns your provider’s goals directly with your own.
A managed cybersecurity provider profits when your systems are stable and secure, not when they break. Their goal is to prevent issues, ensuring maximum uptime and operational continuity for your business.
This shift delivers powerful advantages:
- Budget Predictability: A flat monthly fee eliminates surprise invoices, allowing for confident financial planning.
- Access to Expertise: You gain an entire team of certified security specialists for less than the cost of a single in-house expert.
- Proactive Defense: Threats are identified and neutralized before they can cause harm, dramatically lowering your risk profile.
- Scalability: Services can be scaled to match your business growth, providing a flexible, future-proof solution.
The move toward managed services is a market-wide necessity driven by the rise of cybercrime. The cybersecurity market in the Caribbean, for instance, is growing rapidly, with Security Services leading this expansion. This mirrors global patterns, where the market grew from US$83.32 billion in 2016 to US$166 billion in 2023, largely due to the adoption of managed services. You can read the full Statista market forecast for more details.
A True Partnership for Business Resilience
Choosing a managed cybersecurity partner is about more than outsourcing IT tasks; it's about building a strategic relationship focused on long-term resilience. To better understand this model, you can learn more about what managed IT services are and how they support business goals.
For small and midsize businesses, particularly those in regulated industries, this approach provides enterprise-grade protection that would otherwise be unattainable. It frees you to focus on your core business, confident that a dedicated team is working 24/7 to keep your digital assets safe.
How to Choose the Right Cybersecurity Partner
Selecting a cybersecurity partner is a critical business decision, not just an IT task. The right partner acts as an extension of your team, integrating security into your operational goals. The wrong one can leave you exposed while draining your budget.
To make the right choice, look past sales pitches and evaluate potential partners on criteria that build long-term resilience and support growth. This is not about buying a tool; it's about finding a partner who delivers a comprehensive strategy to reduce risk, ensure compliance, and support your business objectives.
Evaluate Their Industry Expertise
Your first filter should be industry specialization. A cybersecurity firm that understands the unique operational and regulatory challenges of your sector—whether law, healthcare, or finance—is invaluable. Generic security solutions are inadequate for regulated industries with specific compliance mandates.
When vetting a potential partner, ask direct questions about their experience with businesses like yours.
- For law firms: "How do you secure client-attorney privilege in cloud platforms like Microsoft 365?"
- For healthcare clinics: "Describe your experience protecting patient data while ensuring clinical systems remain operational."
- For financial services: "What is your strategy for protecting transactional integrity and preventing sophisticated fraud?"
A partner with relevant industry experience will provide specific examples and case studies. They will speak your language because they understand both the technical threats and their real-world business impact.
Understand Their Service Delivery Model
Not all cybersecurity services are structured the same way. It is important to understand how a potential partner packages and delivers their support. The two most common models are à la carte services and fully bundled services.
The à la carte approach allows you to select individual services, but it can lead to coverage gaps and unpredictable costs. A bundled, fixed-fee model provides a more comprehensive and predictable solution, wrapping everything from threat monitoring to compliance management into one cohesive strategy for a single monthly fee.
This model aligns their incentives with your success. They profit when you are secure, not when you have a problem.
A bundled, fixed-price service model eliminates financial surprises. It ensures your provider is motivated to prevent incidents, not just react to them, turning them into a true stakeholder in your operational stability.
Scrutinize Their Incident Response Capabilities
Even with the best defenses, incidents can still happen. A provider's true value is often demonstrated in how they manage a crisis. Do not just take their word for it—investigate their Incident Response (IR) processes.
A prepared partner should have a clear, documented plan that outlines every step they will take during a security event. Ask for their Service Level Agreements (SLAs), which legally define their response time commitments. How quickly will they act to contain a threat? What are their guaranteed recovery times?
An experienced cybersecurity services company will have well-defined protocols and be transparent about their capabilities. This transparency provides confidence that they can minimize damage and restore operations quickly.
Cybersecurity Vendor Evaluation Checklist
This practical checklist can help you systematically compare potential partners and ensure you are asking the right questions.
| Evaluation Criteria | Key Questions to Ask | What to Look For in Their Response |
|---|---|---|
| Industry Specialization | "Can you provide case studies from our industry (law, healthcare, finance)?" "How do you stay current with our sector's compliance regulations?" |
Specific examples, not generic answers. They should speak your industry's language and understand your unique risks. |
| Service Delivery Model | "Is your pricing a fixed monthly fee or à la carte?" "What's included in your standard package?" |
A clear, all-inclusive, fixed-fee model. This shows they are incentivized to prevent problems, not profit from them. |
| Incident Response (IR) | "Can we see your documented Incident Response plan?" "What are your guaranteed response times (SLAs)?" |
A well-defined, documented process. Firm SLAs that guarantee rapid response and recovery to minimize business disruption. |
| Strategic Guidance (vCIO) | "Do you offer vCIO services to help with long-term technology planning?" "How will you help us build a technology roadmap?" |
A clear commitment to strategic partnership. They should want to help you align technology with business goals for future growth. |
| Client References | "Can we speak with 2-3 current clients in our industry?" | Willingness to provide references from satisfied, long-term clients who can attest to their expertise and service quality. |
Using a structured checklist ensures you cover all bases and select a partner who is genuinely equipped to protect and support your business.
Assess Their Strategic Planning Approach
A top-tier cybersecurity partner does more than manage technology; they provide strategic guidance, often through a Virtual CIO (vCIO) service. A vCIO acts as your high-level advisor, helping you build a technology roadmap that aligns with your business goals.
They help you make informed decisions on technology investments, plan for future growth, and ensure your security evolves with your business. This strategic oversight is what distinguishes a mere vendor from a true long-term partner.
What to Expect from Your Engagement Roadmap
Partnering with a cybersecurity services company is a structured process. A professional firm will guide you through a clear engagement roadmap to build your security foundation, ensuring each step aligns with your business risks and objectives.
The purpose of a roadmap is to demystify the process, turning a technical project into a strategic partnership. It shows exactly how technology will be aligned with business goals to deliver measurable results.

Discovery and Assessment
The process begins with a deep dive into your current environment. This initial phase is about listening and learning. Your partner will conduct a thorough assessment of your existing infrastructure, policies, and workflows to identify vulnerabilities and high-risk areas.
This is more than a technical scan; it's a business-focused analysis designed to understand what is most important to your organization—from critical data and systems to regulatory compliance challenges. The outcome is a clear picture of your current security posture.
Strategic Planning and Design
With a complete understanding of your environment, the next step is to build a tailored security strategy. Your partner will work with your leadership team to create a multi-year technology roadmap. This plan prioritizes actions based on risk and impact, ensuring resources are focused where they will make the most difference.
This strategic phase typically includes:
- Defining clear security goals and metrics for measuring success.
- Designing a security architecture that supports current needs and future growth.
- Developing a detailed project plan with timelines and milestones.
Implementation and Onboarding
With an approved strategy, the implementation phase begins. This is where the planned security controls, tools, and policies are deployed and integrated into your operations. A skilled cybersecurity services company ensures this process is seamless, minimizing disruption to your team.
Onboarding involves configuring systems, training employees on new security protocols, and establishing clear communication channels for ongoing support. An effective partner provides hands-on guidance to ensure a smooth transition. To build a robust defense, it helps to be prepared for worst-case scenarios; you can review our incident response plan template to see what a comprehensive plan includes.
Ongoing Management and Reporting
Cybersecurity is not a one-time project; it is a continuous process of management and improvement. After implementation, your partner transitions to a proactive monitoring and management role. This should include 24/7 threat monitoring, regular system maintenance, and clear performance reporting.
This ongoing partnership is critical, especially in a rapidly expanding market. For instance, the cybersecurity market in Latin America and the Caribbean is projected to grow from USD 22 billion in 2024 to USD 40.11 billion by 2033. This final stage provides the constant vigilance needed to keep your business secure against evolving threats.
Your Next Steps Toward a Secure Future
Choosing the right cybersecurity services company is one of the most important strategic decisions you will make. This is not just about defending against the latest threat; it's about building a resilient organization that can operate with confidence. The right partner looks beyond technical fixes to create a security strategy that supports your business goals.
For businesses in regulated fields like law, healthcare, and finance, the stakes are higher. You need a partner who understands your specific compliance and operational realities. Moving to a managed services model is how you achieve this, transforming security from a reactive cost into a strategic investment in stability and growth. Finding the right fit comes down to a structured evaluation focused on industry expertise, service delivery, and incident response capabilities.
Take a Proactive Stance on Security
The most important step is to understand your current security posture. A thorough assessment is the only way to uncover hidden risks and create a clear roadmap for improvement. Waiting for an incident to force action is a losing strategy. Taking proactive steps today is the most effective way to protect your business.
A consultation with an experienced advisor can clarify your unique challenges and goals. It is an opportunity to explore how a tailored security strategy can reduce risk, maintain compliance, and support your long-term success. The goal is to build a secure foundation that frees your organization to focus on what it does best.
Ready to assess your security posture and build a more resilient business? The team at Tricord I.T Solutions is here to provide expert guidance and help you navigate the complexities of modern cybersecurity. Schedule a consultation with our team today.

