Managed cyber security services are a partnership with an external team of specialists who take responsibility for protecting your company’s digital assets. For business leaders, this means outsourcing the complex, 24/7 job of threat monitoring, detection, and response to a dedicated provider.
This approach provides access to enterprise-grade security expertise and technology without the high cost and complexity of building an equivalent security team in-house. It allows you to focus on core business operations, confident that your data, network, and systems are being professionally managed to reduce risk and ensure reliability.
What Are Managed Cyber Security Services?
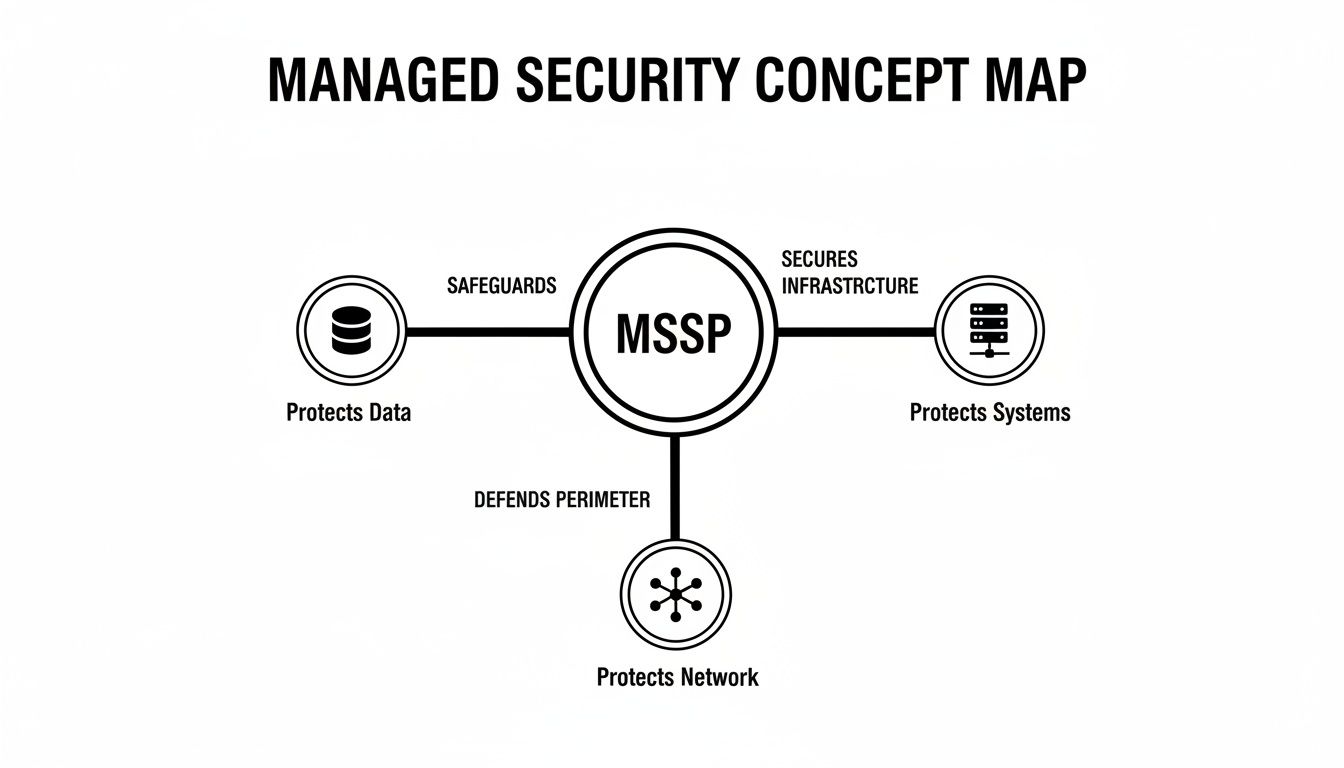
A Managed Security Service Provider (MSSP) acts as an extension of your business, serving as a dedicated partner whose function is to manage and reduce your cyber risk. They provide the technology, expertise, and constant vigilance needed to defend against increasingly sophisticated threats.
This arrangement shifts your security posture from a reactive, break-fix approach to a proactive and strategic one. Instead of waiting for a breach to occur, an MSSP continuously monitors your environment, identifies vulnerabilities, and neutralizes threats before they can cause significant business disruption.
The Shift from In-House to a Managed Partnership
For many organizations, the decision to partner with an MSSP is driven by the significant challenges of managing security internally. An effective internal security program requires:
- Hiring and retaining specialized talent: Cybersecurity experts are in high demand and command high salaries. A single individual rarely possesses all the skills required for comprehensive protection.
- Investing in advanced security tools: Enterprise-grade software for threat detection, response, and analysis can represent a substantial annual investment.
- Providing 24/7/365 coverage: Cyberattacks do not follow business hours. Round-the-clock monitoring is essential for effective security but is a significant operational burden for most internal teams.
Managed cyber security services address these challenges by providing access to a shared team of seasoned experts and a sophisticated technology stack for a predictable monthly fee. This model converts a large, unpredictable capital expense into a stable operational cost.
Comparing In-House IT Security vs. Managed Services
The decision between building an internal security team and partnering with an MSSP has direct implications for your budget, resources, and overall risk posture.
| Business Factor | In-House Security Team | Managed Security Service Provider (MSSP) |
|---|---|---|
| Cost Structure | High, unpredictable capital expenditure (salaries, software, hardware) | Predictable, stable operational expenditure (monthly subscription) |
| Talent & Expertise | Difficult to recruit and retain a full team of diverse specialists | Immediate access to a broad team of certified security experts |
| Technology Access | Requires large upfront investment in enterprise-grade security tools | Leverages a shared, best-in-class technology stack without direct purchase |
| Coverage | 24/7 monitoring is expensive and difficult to staff consistently | Round-the-clock coverage is a standard component of the service |
| Scalability | Scaling security capabilities is slow and tied to hiring or layoffs | Services can be scaled easily to align with business growth or changing needs |
| Focus | Diverts internal resources and leadership from core business objectives | Allows the organization to focus on its primary mission and growth |
For most small to mid-sized businesses, the MSSP model offers a more practical and cost-effective path to achieving a strong security posture.
By outsourcing security, businesses gain not just protection but also operational efficiency. The primary goal is to minimize risk, ensure compliance with standards like PIPEDA, and maintain business continuity without distracting from your strategic objectives.
This partnership is particularly valuable for companies handling sensitive information, such as law firms protecting client data or healthcare providers safeguarding patient records. An MSSP delivers the documented processes and reporting needed for compliance and can help meet the strict requirements of modern cyber insurance policies.
Key Components of a Managed Security Program
A modern security program is not a single product but a system of interconnected layers working together. Each component has a specific function, and their integration creates a resilient defense against cyber threats. Understanding these components clarifies the value of managed cyber security services.
This layered approach is critical because cybercriminals constantly evolve their tactics. A simple firewall is no longer sufficient. Today’s security demands constant visibility, rapid detection, and an expert-led response.
The Core Technology and Teams
A managed security program uses a combination of specialized tools and expert teams to protect your IT environment.
Security Information and Event Management (SIEM): This is the central monitoring hub. A SIEM platform collects, correlates, and analyzes log data from across your network—servers, workstations, firewalls—to identify unusual activity that may indicate a threat.
Security Operations Center (SOC): The SOC is a 24/7 command center staffed by security analysts. They investigate alerts generated by the SIEM, determine if they are legitimate threats, and initiate the incident response process.
Endpoint Detection and Response (EDR): EDR technology is installed on every computer and server (the “endpoints”). It goes beyond traditional antivirus by continuously monitoring for suspicious behaviors and provides the tools to isolate an affected device instantly, containing a threat before it can spread. To learn more, see our guide on what is Endpoint Detection and Response.
Proactive Defense and Active Response
While the SOC, SIEM, and EDR form the foundation of monitoring and detection, an effective program also includes proactive and responsive layers. This shifts your security from a passive stance to actively hunting for and neutralizing threats.
Managed Detection and Response (MDR) is the human-led service that actively investigates and contains threats. When an EDR tool flags a potential issue, the MDR team conducts a deep analysis, hunts for related threats across the network, and manages the entire containment process.
The Importance of Security Maintenance
Responding to active threats is only half the battle. Ongoing maintenance is essential to prevent them from occurring in the first place. This is where vulnerability management and patching are critical.
A modern managed security program excels at mitigating risks, including complex human-factor risks, by implementing robust strategies for proactive insider threat management.
Vulnerability Management is the process of regularly scanning your systems to identify known weaknesses or security gaps. It is like a building inspector methodically checking for unlocked doors or weak windows before a burglar can find them.
Strategic Patching is the process of applying fixes for those vulnerabilities. When a software vendor releases a security update, an MSSP ensures it is tested and deployed promptly to close the security gap before it can be exploited by attackers.
This proactive approach is becoming standard practice. The Canadian cybersecurity services market is projected to grow from USD 8.7 billion in 2024 to over USD 18.7 billion by 2030, with managed services being the fastest-growing segment as businesses turn to experts to defend against escalating threats.
Business Benefits for Regulated Industries
For businesses in law, finance, healthcare, or manufacturing, the consequences of a security incident are severe. A breach can lead to significant regulatory fines, loss of licensure, and irreparable damage to client trust. Managed cyber security services deliver tangible business outcomes that address these high-stakes challenges.
These services are designed to meet the unique pressures of operating in a regulated environment. For a law firm, this means protecting privileged client information under PIPEDA. For a healthcare provider, it means securing patient records to comply with strict privacy laws.
Fortifying Compliance and Reducing Risk
Maintaining compliance is a continuous effort. Regulations evolve, and the burden of proof rests on your organization. A managed security partner helps carry that operational weight.
They provide the necessary tools, documented processes, and consistent reporting that auditors and regulatory bodies require. This enables you to demonstrate that you are actively monitoring threats, managing vulnerabilities, and protecting sensitive data as required.
The real value here is risk transference. When you partner with a specialist, you’re not just outsourcing tasks. You're handing off a significant piece of the risk tied to non-compliance and data breaches, which frees you up to focus on running your business.
For organizations in regulated fields, managed cybersecurity is essential for maintaining standards like those required to be HIPAA compliant. A qualified provider helps implement and manage the technical safeguards that are foundational to these requirements. Our SOC 2 compliance checklist can also serve as a helpful guide in preparing for these standards.
Achieving Cost Predictability and Strategic Focus
A primary financial benefit is the shift from unpredictable capital expenses (CapEx) to a stable operational expense (OpEx). Building an in-house security team capable of managing regulated data involves substantial, ongoing costs for salaries, training, and enterprise-grade software.
Managed services convert these volatile costs into a predictable monthly fee, enabling more accurate budgeting and eliminating the financial shocks of unexpected security investments or incident response. This financial stability is crucial as security becomes a core operational requirement.
Gaining Access to a Virtual CISO
A significant strategic advantage of a mature managed security partnership is access to a virtual Chief Information Security Officer (vCISO). A vCISO provides senior security leadership and advisory services without the cost of a full-time executive.
A vCISO contributes to the business by:
- Aligning Security with Business Goals: Ensuring the security strategy supports organizational objectives, such as market expansion or technology adoption.
- Guiding Technology Investments: Helping make cost-effective, future-proof decisions on security spending.
- Reporting to Leadership: Translating complex security topics into clear business terms for boards or executive teams.
This level of strategic guidance elevates security from a purely technical function to a business enabler that fosters growth, builds resilience, and provides a competitive advantage.
How to Choose the Right Security Partner
Selecting a managed cyber security services partner is a critical business decision. It is not about comparing prices but about entrusting the security and continuity of your operations to a third party. The right provider becomes a seamless extension of your team, while the wrong one can introduce more risk than they mitigate.
A thorough evaluation process is essential to find a partner whose technical capabilities, industry knowledge, and service philosophy align with your company's risk profile and strategic goals.

Evaluate Industry-Specific Expertise
Generic security solutions are often insufficient for businesses in regulated industries. A provider with deep experience in your sector—be it legal, healthcare, or finance—will already understand your specific compliance requirements and operational risks.
Ask direct questions about their experience with businesses like yours:
- Can they provide case studies or references from other companies in your industry?
- Are they familiar with the specific regulations you must adhere to, such as PIPEDA?
- Can their reporting provide the specific documentation required by your auditors or regulators?
Their answers should demonstrate a clear understanding of your operational environment, not just general security principles.
Scrutinize Service Level Agreements
The Service Level Agreement (SLA) is the most important document in the partnership. It contractually defines the provider’s commitments for performance, availability, and, most importantly, response times. A vague or weak SLA is a significant red flag.
The SLA isn't just a technical document; it's a business promise. It should clearly define what happens when an incident occurs, setting measurable expectations for detection, communication, and resolution. This clarity is essential for managing risk effectively.
Review the SLA for specific, quantifiable metrics. Vague promises like "rapid response" are insufficient. Look for guaranteed times to acknowledge a critical alert and firm deadlines for initiating remediation. This ensures you know exactly what to expect during a crisis.
Assess Their Technology and Team
A provider is only as good as their technology stack and their personnel. You can assess their capabilities by asking targeted questions about their tools and their team's credentials.
Inquire about the core platforms they use for SIEM, EDR, and vulnerability management. Ask how they integrate with systems you already use, such as Microsoft 365 and SharePoint. A strong partner can explain the business benefits of their technology in plain language.
The human element is equally important. Verify that their security analysts hold relevant industry certifications (from organizations like NIST or ISO) and ask about their ongoing training programs. A committed partner continually invests in both their technology and their talent to stay ahead of emerging threats.
Understanding Pricing and Total Cost of Ownership
Understanding the financial aspects of managed cyber security is essential for making an informed business decision. It requires looking beyond the monthly fee to consider the total cost of ownership, including the costs you avoid by engaging a specialist.
This represents a shift in perspective: from viewing security as an expense to recognizing it as an investment in business continuity. A well-structured managed security program provides predictable monthly costs, simplifying budgeting and eliminating the financial surprises associated with a reactive, in-house approach.
Breaking Down Common Pricing Models
Managed Security Service Providers (MSSPs) typically offer several pricing models to suit different business sizes and needs.
Per-User Pricing: This model involves a flat fee per employee per month, making costs easy to predict as your team scales. It is well-suited for businesses where user-based activity represents the primary risk.
Per-Device Pricing: For businesses with a diverse range of equipment—servers, laptops, firewalls—this model ensures every critical asset on your network is covered, regardless of the number of users.
Tiered Packages: Many providers bundle services into different levels (e.g., Essential, Professional, Enterprise). These packages group services like EDR, SOC monitoring, and compliance reporting, allowing you to select the level of protection that aligns with your risk profile and regulatory obligations.
Calculating the Total Cost of Ownership
Comparing an MSSP's fee directly to an in-house security salary is a common mistake that provides an incomplete picture. A true calculation of the Total Cost of Ownership (TCO) reveals the hidden expenses of a do-it-yourself approach.
The real financial comparison isn't about subscription versus salary. It's about weighing a predictable operational expense against a host of volatile, often hidden capital and operational costs that come with building and maintaining an internal security program.
These additional costs include:
- Recruitment and Retention: The high cost of finding and retaining certified security experts.
- Continuous Training: The ongoing investment required to maintain team skills.
- 24/7 Shift Coverage: The logistical and financial burden of staffing a round-the-clock security operation.
- Software and Hardware: The significant upfront cost of enterprise-grade security tools and their annual maintenance fees.
The Return on Investment of Managed Security
The ROI becomes clear when you compare these costs against the financial impact of a security incident. A single data breach, extended downtime, or a major regulatory fine can easily exceed the cost of several years of MSSP fees.
This is particularly true for small and medium-sized businesses, which are increasingly turning to managed security services. The market is driven by rising cyber-insurance requirements and the need to avoid business-disrupting breaches. You can learn more about the trends shaping the Canadian cybersecurity market.
When you partner with a provider for services like managed IT support, you are making a direct investment in business resilience and protecting your bottom line.
A Practical Roadmap To Getting Started
Engaging a managed cyber security services partner is a structured process designed to be transparent and manageable. The goal is to build a solution that aligns precisely with your business risks, operational needs, and compliance requirements. It is a methodical journey to establish a strong and sustainable security foundation.
The process unfolds in distinct phases, moving from initial discovery to continuous strategic oversight, all built on a partnership model of transparency and shared objectives.

The Four Phases of Implementation
A successful implementation follows a logical progression to ensure all requirements are met. Each step builds on the previous one, resulting in a comprehensive and resilient security posture tailored to your organization.
Initial Consultation and Risk Assessment
This phase involves a deep dive into your current IT environment. The provider works with your team to understand your business operations, identify critical data assets, and assess existing security controls to find vulnerabilities and compliance gaps.Tailored Solution Design
Based on the assessment, a customized security strategy is developed. This is a detailed blueprint specifying the right technologies (like EDR and SIEM), processes, and response protocols required to address your specific risks and support your business goals.Seamless Onboarding and Integration
In this phase, the plan is put into action. The security provider deploys and configures the necessary tools, integrating them smoothly with your existing IT infrastructure and establishing 24/7 monitoring connections to their Security Operations Center (SOC).Continuous Monitoring and Strategic Reviews
Once active, the service provides constant vigilance. This ongoing phase includes threat monitoring, regular reporting, and periodic strategic reviews to ensure your security program evolves with your business and the changing threat landscape. A key part of this is having a clear procedure, for which our incident response plan template can be a useful starting point.
This roadmap is more than just a technical checklist; it’s the framework for a long-term security partnership. The goal is to build a secure, resilient foundation that lets you focus on your core business with confidence.
If you are ready to explore how this process could strengthen your organization's defenses, a no-obligation consultation is an ideal next step to discuss your specific challenges and goals.
Frequently Asked Questions
Business leaders often have practical questions when considering managed cyber security services. Here are direct answers to some of the most common inquiries.
How does this service integrate with our current IT team?
A managed security service complements your existing IT team, it does not replace it. Your internal team can be seen as general practitioners focused on day-to-day operations and business-enabling projects. An MSSP acts as a team of specialists, focused entirely on advanced threat detection and response. This partnership empowers your internal staff by offloading the significant burden of 24/7 security monitoring, allowing them to focus on core initiatives that drive business value.
What is a realistic timeframe for onboarding?
A typical onboarding process unfolds over several weeks. It begins with a thorough risk assessment to understand your specific environment, data, and compliance needs. Following this, a tailored solution is designed, and the necessary tools, such as Endpoint Detection and Response (EDR) agents, are deployed. The final step is to integrate these tools with the Security Operations Center (SOC) for round-the-clock monitoring. A reputable provider will offer a clear, documented timeline with key milestones.
How are security incidents reported and handled?
When a potential threat is detected, a defined incident response plan is immediately activated. First, SOC analysts investigate the alert to validate it as a genuine threat, filtering out false positives. If the threat is confirmed, they take immediate action to contain it, which often involves isolating the affected device from the network to prevent the threat from spreading. You are notified promptly through pre-agreed channels with clear, plain-language updates on the incident, its impact, and the remediation steps being taken.
Can these services help us meet cyber insurance requirements?
Yes, absolutely. This is a primary driver for many businesses seeking managed security services. Cyber insurance carriers have become increasingly strict, requiring proof of proactive security measures before issuing or renewing a policy. Managed cyber security services provide the exact controls insurers look for, including documented 24/7 threat monitoring, advanced Endpoint Detection and Response (EDR), a formal vulnerability management process, and a tested incident response plan. This partnership provides the documentation needed to satisfy these stringent requirements, often resulting in better coverage and more favorable premiums.
At Tricord I.T Solutions, we don’t just sell services; we build security partnerships that protect your business and clear the way for growth. If you’re ready to strengthen your security with a team of dedicated experts, let’s talk. Schedule a consultation to discuss your unique needs. Learn more at https://bvc.ee2.myftpupload.com.